WeTheNorth is a Canadian market established in 2021 that also serves international users. It offers counterfeit documents, financial fraud tools, hacking and malware services. It has an active forum and community along with an extensive user vetting process.
Is DuckDuckGo An Actual Dark Web Search Engine?
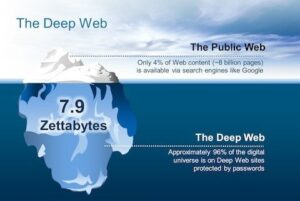
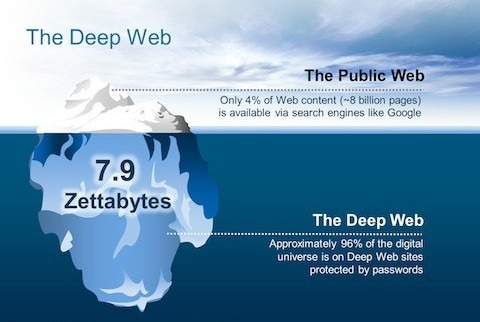
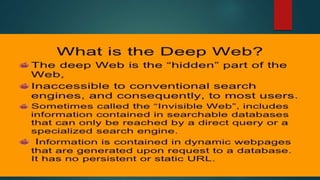
There is no official data available, but most experts agree that the invisible web is several times larger than the visible web. The true size of the internet is unknown, and the same goes for the invisible web. However, the invisible web can be roughly divided into the deep web and the dark web.
Elephind – Search Engine Dedicated To Historical Newspapers
Although profiting from pirated copyrighted material is unethical and illegal, there are some exceptions to using copyrighted material, such as a “private study” provision under UK law. The CIA is contactable on the dark web, providing a completely anonymous way to get in touch with them. However, if you’re communicating with state intelligence agencies, you should use Tor alongside a VPN for maximum privacy. Otherwise, the first node in the onion relay system sees your real IP address, which can be used to locate you and unveil your identity. However, unlike the surface web BBC, the Tor version is accessible in countries like Iran, China, and Russia, with language options in Persian, Mandarin, and Russian.
- While some .onion sites provide essential services like secure communication and censorship-free journalism, others spread malware or run scams.
- Some locations block access to the site, so the New York Times began hosting on the dark web to unblock links to their news and make it accessible to everyone around the world.
- Since these pages would otherwise be behind paywalls, it stands to reason that this would go against copyright laws.
- Wasabi Wallet isn’t free to use, but, for a small fee, you get reliable and anonymous cryptocurrency transactions.
Stay One Step Ahead – Protect Your Data From The Dark Web
Be sure that your experience with Whonix will be comparable to Tor because both programs share the same source code. An easy way to find content on the dark web is to receive a link from someone who already knows about it. Some markets even sell privacy tools, but you are more likely to run across counterfeit prescription pills and stolen identities. The dark web isn’t just one sketchy marketplace hiding in a corner of the internet; it’s more like a messy, unregulated community with everything from freedom fighters to full-blown cybercriminals. Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together. It may initially look abandoned, but the community members will answer your questions.
When viewed through this lens, the dark web’s legality is based on how you as a user engage with it. You might fall to the wayside of legal lines for many reasons that are important for the protection of freedom. Others may act in ways that are illegal for the protection and safety of others. Let’s unpack both of these concepts in terms of the “dark web browser” and the websites themselves. The Internet is sizable with millions of web pages, databases, and servers all run 24 hours a day. But the so-called “visible” Internet (aka surface web or open web) — sites that can be found using search engines like Google and Yahoo — is just the tip of the iceberg.

Explore The Dark Web More Securely With A VPN
These sites use “.onion” domains, which are made up of random letters and numbers up to 56 characters long. Dark web websites won’t show up on Google, but they are indexed by dark web search engines such as Torch. When delving into the dark web, maintaining stringent security and preserving your anonymity aren’t just advisable—they’re essential. Threats here range from malicious actors looking to harvest your personal data to hidden exploits designed to compromise your system. A careless misstep can lead to exposure, malware infection, or worse.
Ready To Explore Web Data At Scale?
Cryptocurrency miners and other malicious software often target dark web users. Using a reliable antivirus to scan your device is worthwhile if you spot suspicious spikes in system resource usage. This isolates any potential malware and prevents cross-contamination with your personal data. Using Tails OS can further security, as all your data is reset every time you close the device. KeyBase combines encrypted messaging with secure file sharing and identity verification. Its dark web version provides the same functionality as the clear web option, while adding Tor’s anonymity layer.

If you make use of a password manager, then it may come with a feature that monitors the dark web for mentions of your email address and password, or any other personal details. It’s something built into the password management services offered by Apple and Google as well, so you don’t need to trawl through data leaks manually yourself. Hackers spend a lot of time on the dark web, and it’s not too difficult to get access to hacking tools and data leaks in this part of the internet. However, it’s much harder to get at the people who are doing the uploading and downloading.
What Is The Surface Web?
Accessing the dark web is legal in itself; the nature of the activities you engage in ensures it stays that way. Criminals prefer the dark web because it offers anonymity like never before. But as long as you don’t knowingly engage in illicit activity on the dark web, you are completely fine. We ensured that the dark web sites we chose had reviews and feedback from real users on other forums; this way, we can be sure of the site’s reliability and legitimacy. The developers of ProtonMail recommend using the Tor browser to visit the dark web version of the service. This ensures greater security and privacy, making it much more difficult for snoopers to get in.
Allows for as many as 5 additional addresses, allows users to manually decide the fee although it’s set at a minimum of 0.4% and maximum of 4%. Also lets users set the time-delay manually which can be set at a minimum of 0 hours and maximum of 24 hours. Also lets users skip the manual setup and rather just click on the “Randomize” button.
Based on our observations from analysis on dark web data using Lunar, we’ve identified the top 7 marketplaces on the dark web in 2025. We developed Lunar to monitor the deep and dark web, including dark web marketplace sites. Download Tor Browser to experience real private browsing without tracking, surveillance, or censorship.
It offers a Reddit-like interface, where you can learn everything you need to know about darknet websites and spotting the real from the scammers. For the record, there are more scam sites for every genuine one, and it’s good to have a discussion forum about this. Switzerland-based Proton (formerly ProtonMail) is one of the most secure email services, and has a reputation for not logging IP addresses. If you care about your privacy on the Internet, no other site comes close.
Can WiFi Owners See Your Internet History?
Privacy advocates frown upon it because of the way it harvests data and profiles users. These concerns are valid because using Facebook undoubtedly exposes users to some of the highest levels of surveillance capitalism anywhere on the web. Tor provides truly anonymous and untraceable browsing and messaging, as well as access to the so called “Deep Web”. We always recommend using a reliable VPN when accessing the deep web or dark web.