Law enforcers can use custom software to infiltrate the dark web and analyze activities. You could be monitored closely even if you are not doing anything illegal. If the above average Joe’s explanation isn’t enough for you, below are some legitimate reasons to use the Dark Web in a bit more detail. Tor anonymity comes with a cost since malicious hackers and criminals like to operate in the shadows. For example, perpetrators of trafficking and cyber attacks use the dark web to disguise their actions.
Usar Una VPN Para Aumentar La Privacidad
To contribute a tip, join the community, which can be done anonymously through an approved onion link. The site is strongly resistant to hackers and encrypts your data in transit as well as the rest. Among many open-source whistleblower sites, SecureDrop is currently a leading platform.
Best 5 Closed Hidden Services On Tor

They use pseudonymous wallets, privacy coins (like Monero), mixers, chain-hopping, and non-KYC platforms to obscure transaction trails. Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums. Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement.
Does The CIA Have An Onion Site?
These pages can also help circumvent some forms of government censorship. AVG Secure VPN masks your IP address from other internet users, the websites you visit, and even government surveillance. And thanks to ultra-secure, end-to-end encryption, your online activity is obscured. While it may have a reputation for seedy and dangerous content, many dark web websites are legitimate and useful resources. Keep reading for a rundown of the best dark links you might want to check out.
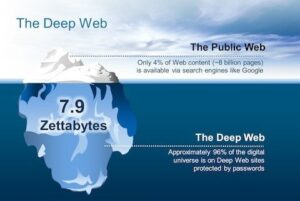
Surface Web Vs Deep Web Vs Dark Web Vs Darknet
Many deep search engines prioritize user privacy, but not all of them offer the same level of security. Some may inadvertently index harmful content or fail to protect your data. This makes it crucial to choose search engines with robust privacy protection features.
Mail and packages addressed to a PO Box will be held securely at the post office until the box holder retrieves them. PO Boxes can be rented for various periods of time, depending on the postal service’s policies and fees. As an alternate, the network contains willing participants who agree to the rules and protocol.
Ensure Compatibility With Privacy Tools
It’s particularly useful for sensitive communications that need to remain private. TorLinks maintains one of the most reliable directories of verified .onion sites. Its strength lies in regular updates and community-driven verification of links. I especially like how TorLinks categorizes links based on their type, letting you easily find what you need. In some ways, dark web websites offer more browsing freedom, but the lack of safeguards can leave you exposed to hackers, malware, and other online threats, like viruses or other malware. The lack of regulation leaves the dark web rife with offensive content and unsafe websites.
Alt Address
The search engine excels at indexing a wide range of content, from forums to marketplaces. Its advanced algorithms deliver accurate search results, helping you find relevant information quickly. NotEvil is particularly useful for research purposes, as it provides access to resources that are often overlooked by other deep search engines.
PageOn.ai excels in generating conversational content tailored to your needs. Its AI-powered tools streamline the content creation process, saving you time and boosting efficiency. Whether you’re preparing a presentation or conducting research on the invisible web, this feature ensures your output resonates with your audience. Users have reported a 25% increase in success rates for marketing pitches, highlighting the platform’s ability to deliver impactful results. The invisible web is a treasure trove of information, but it also harbors risks. Malicious links are a common threat, and clicking on them can expose your device to malware or phishing attacks.
This means you have to know someone who is already using the platform. Even without the code, you can visit the security section to get tips on improving your daily life privacy. This service is a good source of statistics if you have a school project requiring research on Tor and the dark web.
- To reduce this risk, use the Tor Browser properly, keep your software updated, avoid sharing personal information, and pair it with a reliable VPN.
- Because the Hidden Wiki aggregates many links, it often contains outdated or malicious URLs disguised as legitimate ones.
- Onion sites are considered part of the deep web because search engines like Google and Bing can’t index them.
- We are not responsible for any harm or loss you may receive by following links listed on this site.
- Always cross-check the information you find, especially when accessing academic or investigative resources.
- First, rely on community-vetted sources and updated link lists from trusted forums like Dread or The Hub, where users report scams and share verified onion addresses.
With the above dangers, it’s imperative to tread carefully as you step into the dark web. Its source of funding is the deep wallet of the Sandler Foundation and various other similar organizations. We check all comments within 48 hours to ensure they’re real and not offensive. Some sites might use these details for advertising, analytics, or tracking your online preferences. However, the technology that Yippy manages, was created in Carnegie Mellon.
- Additionally, OSE provides the “last update” date for each URL, enhancing user transparency and trust.
- This technology is particularly useful for academic research and investigative journalism.
- Also, be wary of RATs (Remote Administration Tools) that malicious actors might try to install through dark web sites to gain control of your system.
- Some may log search history, contain hidden scripts, or other elements that can jeopardize user anonymity.
- Hence, if you participate in them, whether knowingly or unknowingly, you can end up putting criminal charges on yourself, and in some extreme cases, even imprisonment.
Engaging with the dark web securely requires preparation, awareness, and the right tools. Here are some of the ways to reduce the risks that come with using the dark web. Get on the Dark Web (GOTDW) is your go-to guide and safe search engine for exploring the dark web responsibly. The project is widely regarded as a cornerstone of internet anonymity, supporting activists, journalists, and individuals in restrictive regions worldwide. The Dark Web isn’t a place for everyone but it’s worth exploring some parts of it. For those who may be a little faint of heart – we have listed 50 Legit Dark Web sites you can visit.

Pro Tip: Use A VPN To Stay Safe When Using The Dark Web Search Engines
It’s a wallet, explorer service, not a dark web marketplace itself, but still a helpful resource. In some countries, such as China and North Korea, the government uses heavy online censorship and blocks many dark web websites. This is where an Onion website, like the Tor browser, comes in handy. The dark web is a part of the internet that you only step into with a specific tool (Tor, more on this later in the article).
We’ve compiled an up-to-date list of the best onion sites so you can get a taste of what’s out there. Launched after the takedown of AlphaBay in 2021, Abacus Market has rapidly risen to prominence. It features over 40,000 listings including narcotics, counterfeit items, hacking tools, and stolen data. The marketplace is well-known for its bug bounty programs and robust security mechanisms, including mandatory 2FA. Dark web markets have exploded in scale and reach in 2025, becoming the most dangerous hubs for trading drugs, stolen data, and hacking tools.