Through the targeted use of our proprietary AI bots, we are able to infiltrate relevant darknet markets and perform real-time speech analysis. This enables us to identify transactions and actors that are of importance to our clients. As soon as a suspicious case is identified, our specialized darknet monitoring team is informed.
Related Content
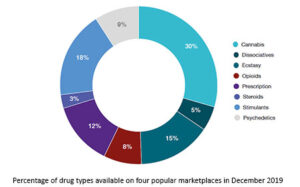
When the FBI arrested Ulbricht in 2013 for money laundering and drug trafficking, among other offenses, the criminal complaint revealed the marketplace had generated over $1.2 billion in just two years. A handful of dark web search engines that do index .onion sites include NotEvil, Ahmia, Candle, and Torch. Western drug flows in particular come from US-domiciled exchanges and trace flows from those to darknet markets. The entity “DNM Aggregator” that appears within each category refers to a service we’ve identified as being in control of multiple, disparate darknet markets.
Tordex Search Engine
Surprisingly, most guns on the darknet actually start as legal products. The UNODC (United Nations Office on Drugs and Crime) maintains that almost all firearms are originally manufactured through legal means. So, what even is this dark web, and why are these marketplaces present there? Purchases through links on our pages may yield affiliate revenue for us.
Added Security: Use A VPN
Much like with drug sales, a similar pattern of task differentiation emerged among darknet markets providing cybercriminal services. As for cybercriminal administration, the category includes inflows from ransomware affiliate wallets. This includes purchases such as malicious software and supporting services which cybercriminals sometimes make using escrow services on crime forums.

Cryptocurrency Transactions

It’s something built into the password management services offered by Apple and Google as well, so you don’t need to trawl through data leaks manually yourself. Even if you’re using a private, anonymized crypto wallet, there are other ways your identity can be revealed—even if it’s something as simple as letting a personal detail slip in an instant message. A VPN enhances your privacy and security by encrypting your internet traffic and masking your IP address, making it difficult for anyone to track your online activities on the dark web. In addition to these main categories, there are other sub-forums, such as Games, which specializes in leaks of game codes, plugins and other gaming-related content. The Other Leaks section also enables the sharing of various data leaks that do not fall directly into the other categories.
Key Cyber Threats Facing The Financial Sector In 2025

Nemesis users were not allowed to conduct transactions in official, government-backed currencies. While there are many sites that facilitate illegal activities, there are also legitimate sites that provide valuable resources, including educational materials and tools for privacy protection. After the cyberattack on the Bernese IT company Xplain in May 2024, stolen data was published on the darknet. An analysis by the Federal Office for Cybersecurity (BACS) revealed that around 65,000 of the 1.3 million data records published were relevant to the Federal Administration. The hacker group Play, which was responsible for the attack, had captured 900 gigabytes of data. As Xplain did not respond to the ransom demand, the data was published on the darknet.
- As cyber-criminals embrace new technologies it’s becoming increasingly necessary for security professionals to do the same in order to stay ahead.
- A VPN hides the fact that you’re using Tor, which is blocked in some countries and always raises doubts because of its criminal reputation.
- So, even though it does exist on the internet, Google doesn’t index any of these pages or content.
- As a user or cybersecurity professional, approaching these marketplaces demands utmost caution, thorough knowledge of operational security, and constant awareness of legal boundaries.
- A VPN enhances your privacy and security by encrypting your internet traffic and masking your IP address, making it difficult for anyone to track your online activities on the dark web.
- These hidden networks provide a platform for illegal activities that include the sale of stolen data, hacking tools, weapons, counterfeit currency, and narcotics.
Top Cybersecurity Discord Servers To Join

Law enforcement may not be able to eliminate illicit activities from the dark web, but could be at least slowing it down. This would be significant news if that were the case as this would mean that deterrence is possible in this ecosystem. The next few months will definitely be interesting to improve our understanding of how police operations shape the future of the dark web.
- They also include user reviews and ratings, helping newcomers identify trustworthy vendors and avoid scams.
- This service is a good source of statistics if you have a school project requiring research on Tor and the dark web.
- DarkOde Reborn is a great darknet market where you can find anything you want.
- In this era, it takes one wrong click and all your sensitive data ends up in the wrong hands.
- They’re strict—no fentanyl or ransomware—which suits folks who like cleaner trades, a nod to the decentralized shift.
Purchasing or selling illegal goods—such as controlled substances, counterfeit documents, or stolen data—can result in significant legal penalties, including fines, criminal charges, and imprisonment. Even users who access these platforms without intent to buy illegal items risk suspicion or investigation. A high degree of security measures further safeguards users on dark web marketplaces. Buyers and sellers alike use encryption tools, fake identities, and VPNs to add extra layers of protection. These markets employ robust protocols that protect transactions from law enforcement, making it challenging for even the most skilled cyber professionals to trace activity back to its origin.

Pirate Bay, a BitTorrent site that law enforcement officials have repeatedly shut down, is alive and well there. We don’t want to leave you with the impression that everything on the dark web is nefarious or illegal. The Tor network began as an anonymous communications channel, and it still serves a valuable purpose in helping people communicate in environments that are hostile to free speech.
Law Enforcement Often Extracts Metadata From Seized Servers
According to the most recent survey on the use of technologies that enable access to the Dark and Deep Web, India had the highest percentage of users at 26%. Russia was second, with 22% of local netizens saying they have used tools like Tor to access the Deep Web. Brazil (21%), Indonesia (20%), Turkey (16%), South Africa (16%), and Sweden (16%) all made the top five. At 10%, the US ranked 11th — the same as Australia, Hong Kong, Germany, and Japan. Deep Web stats from 2023’s third quarter reveal that Iranians made up 24.44% of Tor’s bridge users, while people from the United States accounted for 15.08%.
Security And Anonymity Features
Most e-commerce providers offer some kind of escrow service that keeps customer funds on hold until the product has been delivered. Every communication is encrypted, so even the simplest transaction requires a PGP key. The affiliates distribute the ransomware packages through the dark web. These attacks often include stealing victims’ data and threatening to release it on the dark web if the ransom isn’t paid. These groups develop their own sophisticated malware, sometimes combined with pre-existing tools, and distribute them through “affiliates”. The dark web is a subset of the deep web that is intentionally hidden, requiring a specific browser—Tor—to access, as explained below.
Its interface makes it easy to identify clone websites and ensures that users always use the authentic site. Vice City Market is a new and cutting-edge dark web marketplace where you can find a range of products and vendors at an affordable price (compared to the damage they do to the victims). To access this marketplace, you must register, but before that, you must verify yourself as a human by passing a CAPTCHA test.
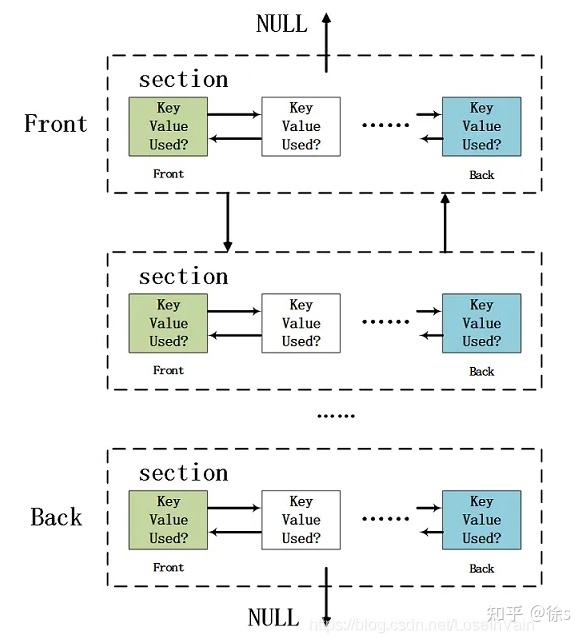
Though the sanctioning and closure of fraud shop Genesis Market occurred last year, there were no other sanction events for the darknet market ecosystem, or major market takedowns. We’ll continue monitoring darknet market trends in 2024, and are curious to see what new tactics markets and fraud shops may employ to find more customers. Kraken Market also captured the largest share of transfers potentially sent for the purpose of obfuscating funds, as well as buying illegal products. In addition to that activity, markets like these host vendors that advertise their own cashout or swapping services, resulting in tens of millions of dollars in laundered funds. BreachForums is divided into several sections that focus on specific types of data breaches.
ExpressVPN had created a .onion version of its website to allow greater privacy and anonymity for Tor browser users. The invisible web is made up of data and information that is not indexed and cannot be searched for by using traditional search engines. Content includes non-indexed websites, apps, and resources, which can include protected information such as, online banking, specialized databases, non-linked and password-protected websites, and more. It includes media and archives which cannot be crawled and indexed with current search engine technology.