The website has an advanced search filter and an easy-to-use interface, which makes it easy to find what someone is looking for. Check out these best onion sites to access the dark web securely and anonymously. Tor’s elaborate onion routing technique makes web tracking extremely difficult, but it’s still possible for third parties to spy on certain aspects of your web activity.
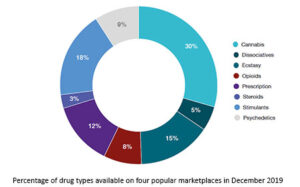
What Kind Of Content Is On The Dark Web?
SecureDrop is a secure platform used by journalists and whistleblowers to anonymously share sensitive information via the dark web. The most common tool is the Tor browser, sometimes used with a VPN for additional anonymity and protection. Offering books for free, shadow libraries face the morality question of copyright vs. access to information and knowledge. Just Another Library is one such service, with a wealth of books covering computer programming, science, and niche hobbies (sailors’ knots, anyone?).
Deep Search
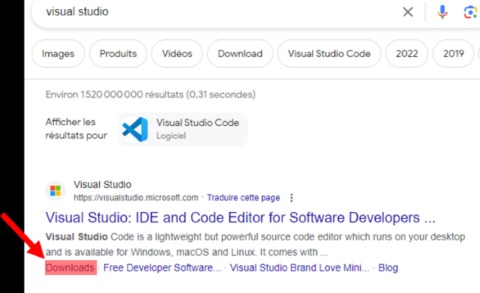
The dark web is intentionally hidden from surface web indexing, and to access it, you need a specialized dark web browser, like the Tor browser. If one tries to visit the dark web with a regular browser, there will be no web pages to visit. Since the dark web is hidden from the surface web, these dark web search engines allow users to explore the concealed part of the Internet. Unlike traditional search engines, it organizes dark web links into specific sections, making it easier to navigate and explore different parts of the dark web. Unlike other dark web search engines, DuckDuckGo doesn’t index illegal content, focusing instead on providing safe, unbiased results. Torch is one of the oldest and most well-known dark web search engines, providing access to a vast index of .onion websites.
The Top 5 Dark Web Search Engines
- Run Tor in a sandboxed environment (e.g., Tails OS on a USB drive) to isolate activity from your main system.
- However, it is crucial to use Torch responsibly and within legal and ethical boundaries to ensure a safe and secure online experience.
- The dark web is a hidden part of the internet that requires specialized software to access.
- Again, people who live in countries where the freedom of the internet is limited, for example in China, can really benefit from using Tor.
It stands as one of the most prevalent search engines utilized within the TOR Browser ecosystem. DuckDuckGo presents a straightforward interface reminiscent of Google’s, featuring a search box at the center of the page where users can input their queries to retrieve relevant results. The deep web is just the part of the internet you can’t find with a search engine.
What Is The Deep Web?
However, it’s worth noting that Candle struggles to interpret certain characters like parentheses or quotation marks, posing a limitation to its functionality. Its user-friendly interface makes navigation a breeze, offering uncensored and unrestricted web search results. However, this lack of censorship increases the likelihood of stumbling upon malicious websites. Despite this, Torch’s impressive speed ensures minimal waiting time for page loading, enhancing the overall user experience.

OnionDir: The Clear Net Directory Of Tor Onion Sites
This makes them essential for accessing unindexed content like whistleblower platforms, but they require Tor Browser for access and carry higher privacy risks if not used securely. New engines like VormWeb categorize results by safety (secure, moderate, risky), a trend likely to dominate by 2026. NotEvil could evolve its filtering to include trust scores, leveraging community reports and AI to flag phishing or malware-laden sites. NotEvil’s free-only model offers a safe, broad alternative but lacks the depth or features of Haystak’s premium plan.
ICEBERG Deep Onion Search Engine
However, many present uncensored search results in their rawest form and expose users to a flood of stolen data, compromised credentials, and black market activity. While these platforms should never be used casually or without proper precautions, they offer unique visibility into potential threats that may otherwise go unnoticed. Dark web search engines are specialized tools that allow users to perform web searches within the dark and deep web. Unlike traditional search engines like Google or Bing, these tools operate on the Tor network — a hidden ecosystem where most content is intentionally obscured from public view.
Exploring the dark web requires specialized knowledge and tools due to its anonymous nature and the use of encryption to maintain user privacy. It’s important to note that while the dark web can be used for legitimate purposes, such as protecting the privacy of activists and journalists, it can also host illegal activities. Therefore, caution and awareness of legal implications are paramount when accessing it.
Moreover, due to its popularity, many copycats of the Hidden Wiki exist. So don’t be surprised if you encounter different versions that claim to be genuine, and be very careful. Purchases through links on our pages may yield affiliate revenue for us. We review and list tools and products without bias, regardless of potential commissions. Install Avast SecureLine VPN to encrypt your internet connection and protect your privacy wherever you go online. Download Avast SecureLine VPN to encrypt your internet connection and protect your privacy wherever you go online.
Keep in mind that you’ve to use very specific keywords when searching. And most importantly, be patient as you’ve to sort through a lot of useless results. These search engines work best if you already know what site you’re looking for, not for general browsing. The biggest and most frustrating part about dark websites is that they live for a short span of time. These platforms keep changing their addresses to avoid DDoS attacks or law enforcement agencies.

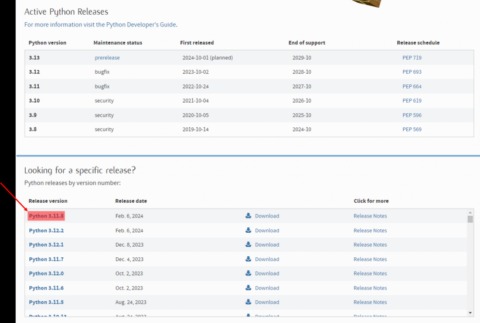
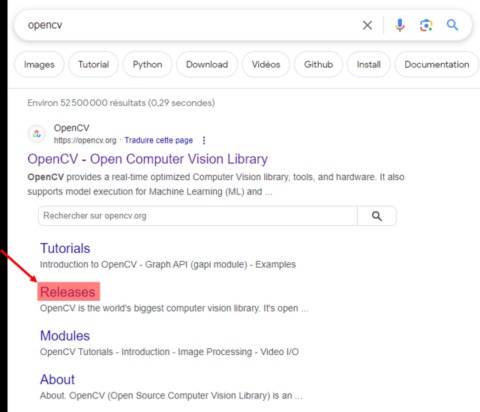
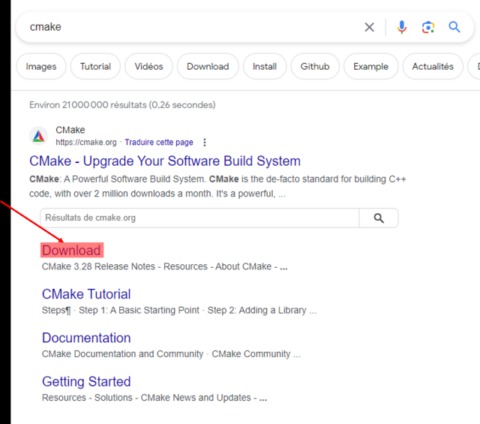
So, once you’ve activated your VPN and your privacy is secured, it’s time to visit Tor’s official download page. Make sure that when you download the Tor file, it’s from their official website. It’s impossible to access the dark web with a regular browser like Chrome or Safari. But again, your ISP won’t be able to see any of the content you’re reading or what you are sending and receiving through the Tor network.
Why Do Dark Web Search Engine URLs Keep Changing?
Data gleaned from ransomware and data breaches is available on the dark web. Millions of customers’ personal data, including names, addresses, bank account and credit card account information, and many other forms of sensitive data. The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information. Again, people who live in countries where the freedom of the internet is limited, for example in China, can really benefit from using Tor. Later on, the underlying Tor code was released into the wild under a free license, leading to the formation of the Tor Project.
ThreatMon’s Deep/dark web monitoring service provides proactive identification and monitoring of compromised corporate data, sensitive information, or credentials on the dark web. Threat Intelligence roams the dark web, analyzes criminal activity, and gathers clues for its purpose. It monitors dark web forums and marketplaces related and monitors postings.