Ransomware as a service, stealer malware as a service (SMaaS), and phishing-as-a-service operations are thriving and helping fuel illicit add-on services. There are also myriad support services that help lower the barrier to entry in executing these attacks, or to help make attacks more efficient. These include crypting services, dropper services, and exploit kits for RaaS and SMaaS, according to Carroll.
Freebie VPNs will track their users’ online usage, as they make money by selling this tracking info to advertisers and other nosy parties. While the iOS solution is not an official one, the Tor Project links to it, providing the browser its tacit approval. We’ve also looked at how Tor allows users to access the dark web, and we’re now aware of the resources and dangers that await us there. The dark web is a very popular platform for journalists, political bloggers, and political news publishers, especially for those living in countries where strict censorship shields are the rule. Using a VPN in conjunction with the Tor Browser is an excellent way to keep your online travels secure and private.
What Is The Best VPN For Tor?
It is often offered in some portals to give threat actors the tools for cyberattacks. However, it also lingers all across the dark web to infect unsuspecting users just like it does on the rest of the web. As such, the dark web has attracted many parties who would otherwise be endangered by revealing their identities online. Abuse and persecution victims, whistleblowers, and political dissidents have been frequent users of these hidden sites. But of course, these benefits can be easily extended to those that want to act outside of the constraints of laws in other explicitly illegal ways.
The Ultimate 2025 Guide To The Tor Browser
The clear web, also known as the surface web, consists of websites and services that are indexed by search engines and accessible through standard web browsers. It includes everything from news sites and social media platforms to online stores and streaming services. The clear web is regulated and monitored by various governments, making it relatively difficult for people providing illegal content and services to operate on the clear web.
Dark Web Tools & Services

Rule No.41 allows a federal judge to issue a search and seize warrant for any person who is using anonymity software like Tor. Then, simply click the operating system that you are using and download the file. While an iOS version of the official Tor browser is not available, there are Tor-compatible browsers available in the App Store. Make sure that when you download the Tor file, it’s from their official website.
- And all the Dark Web sites have weird domain addresses and end in .onion suffix so that they are much harder to track and only accessible by Tor.
- Understanding that the nature of the internet meant a lack of privacy, an early version of Tor was created to hide spy communications.
- You may very well end up in the middle of a stakeout that could turn ugly.
- To get started, visit the Tor Project website and download the Tor browser.
- China uses what is known as the “Great Firewall” limit access to popular sites for this exact reason.
This is why I strongly advise anyone visiting the dark web to exercise the greatest of caution during their dark online travels. Check out my article for more information about the dark web and how to access it while staying safe. One way to stay safe is to use a VPN while accessing the dark web, so be sure to check out my article on the best VPNs for the dark web. In addition, NordVPN offers Onion over VPN (think Tor over VPN), which routes your internet traffic through one of its servers, passes it through the Onion network, and then sends it to the internet. This means you can use your favorite browser instead of the Tor Browser and still benefit from being routed through the Onion Network.
What Is The Dark Web? Here’s Everything To Know Before You Access It

But the process is not as simple as that, there are safety measures and privacy concerns that should be taken into consideration. These techniques, over time became public and thus led to the emergence of the hidden networks. As the features of dark web tools developed, the criminal mind saw the possibility of anonymous trade, leading to markets. Another challenge of finding dark web sites is that they don’t often last long. Many sites become defunct quickly, either because they are shut down due to illegal activity, their founders lose interest, or they change addresses and names to avoid detection. In January 2024, a huge data leak exposed the names, phone numbers, addresses, and Aadhaar details of 750 million Indian telecom users.
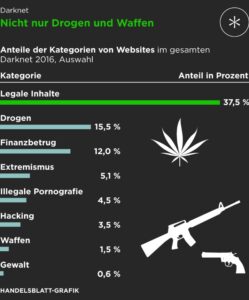
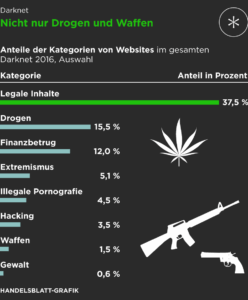
Drugs: The Flagship Category

The Tor network began as an anonymous communications channel, and it still serves a valuable purpose in helping people communicate in environments that are hostile to free speech. “A lot of people use it in countries where there’s eavesdropping or where internet access is criminalized,” Tiquet said. The Deep Web consists of countless legitimate applications, such as research or retrieval of personal medical records, or corporate management of data. Researchers generally use databases like JSTOR for articles, while healthcare providers maintain private information regarding patients in secure systems. Many organizations employ the Deep Web for secure data storage and communication. In this way, the Deep Web is a constituent part of today’s Internet usage.
This allows you to use the computer without the risk of corrupting your computer’s normal operating system with viruses or malware. Tails also protects you from possible malware, viruses, or keystroke loggers that may have already infected the computer, as it doesn’t run the operating system already installed on the device. Keep in mind what you’re looking for, find that information, and disconnect from the dark web. As enticing as it might be, don’t follow links to other parts of the dark web.
Potential Risks And Threats On The Dark Web
Data brokers such as LocalBlox for instance crawl the web and store information about business and consumers to sell for marketing purposes. In order to understand the dark web properly, you need to understand that the internet is a huge and sometimes disorganized place. It has billions of sites and addresses, it is amazing that we can both search for – and find – anything. Why else would the police in Brazil, Germany, and the United States need to raid dark web e-shops like the Wall Street Market and the Silk Road? Charging the operators with a long grocery list of crimes ranging stolen data, drugs, and malware. These things do happen on the dark web, but they are one piece of the jigsaw.
How Does The Tor Browser Work?
In looking at how you access the dark web, one must consider the cords that are plugged into their devices. The use of dark fiber cables can grant users a clutter-free web experience for a faster, more discreet web browsing session. Typically these are utilized by businesses, but if someone wanted to go dark, this would be something to consider. Dark fiber pricing is usually done through leasing from service providers.

Despite the ominous-sounding name, the Dark Web leverages encryption, volunteer relay nodes, and hidden domain systems that do not conform to conventional address resolution. Such architecture helps websites and services obscure their physical server locations. The Dark Web is not easily accessible and one has to go through some extra steps to locate it. Unlike other conventional browsers, it is impossible to type .onion addresses directly. However, there are browsers that are developed for the dark web, such as the Tor Browser.
How To Access
“The Tor network is another network which sits on top of the TCP/IP internet, stitching the participating computers together into a wholly new network ‘space’, not IPv4, not IPv6, but ‘Onion Space’.” The dark web is dangerous due to the presence of scams, malware, and illegal material. The use of tight security measures, dedicated hardware, and awareness are required to prevent these threats. Tor Browser versions for Android and iOS allow smartphone users to access.onion sites. However, extra caution is advised—use a good VPN and ensure the security settings of your device are up to date to minimize risks. SentinelOne’s Singularity Endpoint continuously monitors system activities, file changes, and other critical processes to protect against malware and dark web security threats.