Stick to verified dark web directories and legitimate services to minimize your exposure to risks. To make...
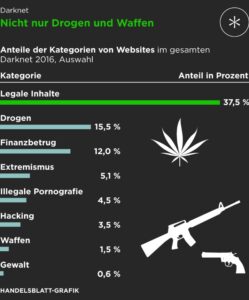
Unlike traditional e-commerce websites, these marketplaces rely on encrypted networks like Tor (The Onion Router) and cryptocurrencies...
You can also limit your risk by being picky about your ATMs, where criminals sometimes install card...
The 2013 Yahoo data breach is a classic case of how security flaws and weak encryption can...
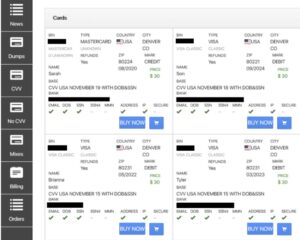
Card checkers are tools used by threat actors to verify the validity and authenticity of credit card...
The court heard the defendant told officers it was “proper money” and claimed it was legal and...
One key difference between Tor and I2P is that I2P bundles its data packets together into “cloves”...
It is a wallet-based shop, meaning you must first deposit bitcoins into your wallet before purchasing any...
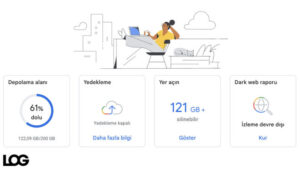
Freezing your credit reports limits access to your reports and keeps creditors from checking your credit in...
For example, state-level actors can execute traffic correlation attacks, wherein they monitor both incoming traffic at the...