Sci-Hub is a massive database that eliminates the barriers to getting scientific knowledge. It contains millions of scientific research documents from around the world. The site seeks to liberate information by making it free to individuals and institutions. Moreover, due to its popularity, many copycats of the Hidden Wiki exist. So don’t be surprised if you encounter different versions that claim to be genuine, and be very careful. Purchases through links on our pages may yield affiliate revenue for us.
Experience The World’s Most Advanced Cybersecurity Platform
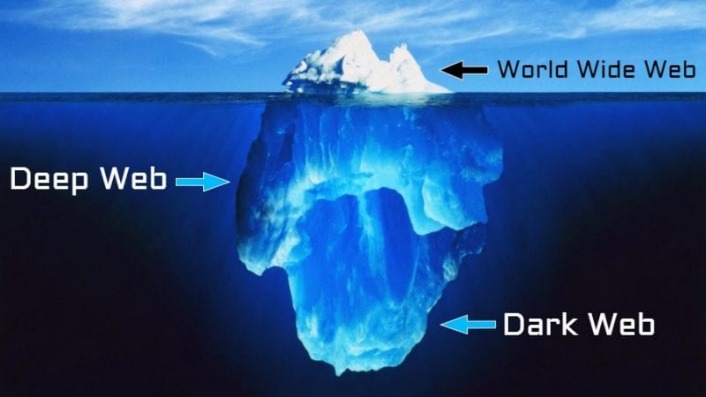
The Deep Web refers to parts of the internet that aren’t indexed by standard search. These aren’t hidden for nefarious reasons, but rather to protect sensitive or personal information. This allows you to use the computer without the risk of corrupting your computer’s normal operating system with viruses or malware.
- Due to limited accessibility, we are generally unaware of the relative scale of the deepweb and darkweb in comparison to the surface web.
- Tor and the dark web provide total anonymity from an internet connection standpoint, but an IP address is only one way you’re identifiable online.
- The Onion Router (TOR) technology used by the TOR browser and the Dark Web was created by a project funded by the US Naval Research Lab (NRL).
- This type of scam is incredibly prevalent on the Dark Web, making it extremely easy for criminals to defraud people.
- These are the primary sources of what the general public thinks of as “dark web.” Online marketplaces selling hacked credit cards, fake passports, malware kits, untraceable drugs, anything.
How The Deep Web Is Different From Traditional Internet
The surface web hosts most online activity; hence, it would be a very lively space for the exchange of information and commerce. Users often turn to the dark web for private communication, whistleblowing, or accessing restricted information in censored regions. However, it’s also notorious for hosting illegal activities, including illicit marketplaces and hacker forums. Most internet users browse content online using the surface web, a segment of the internet where sites are indexed by popular search engines and can be easily viewed using traditional web browsers. While the surface web may represent most of what the average user sees, there are many more layers of hidden content to be found on the dark web.
Legal Uses Of The Dark Web

Hence, while the face of the internet remains the surface web, the deep and dark web are the hidden layers of the internet that require caution and understanding to traverse. Most internet users access deep web content daily without recognizing the distinction. The dark web serves as the primary distribution channel for cybercriminal enterprises. When examining what is dark web used for, we find both legitimate privacy protection and unfortunately, a range of illicit activities. In general, the rules for accessing the deep web and the dark web safely are similar to the best practices for accessing the surface web.
Accessing The Dark Web Requires A Specific Browser
To access the Dark Web safely, use the official Tor browser and consider utilizing a VPN to enhance your privacy by encrypting your internet traffic, preventing tracking by ISPs or government entities. Before you dive into hidden layers of the web, secure your visible ones. Stay informed, stay protected, and choose tools that align with your values. It’s a place where activists fighting for freedom and criminals exploiting vulnerabilities can coexist—sometimes on the same platform. What you find depends heavily on where and what you’re looking for.
Best Browsers For Accessing The Deep And Dark Web
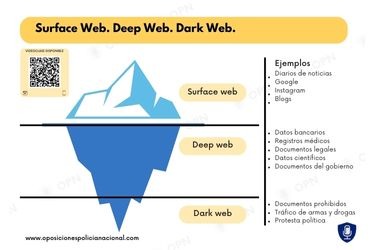
Unlike the largely legitimate Deep Web, the Dark Web has gained notoriety for hosting sites involved in illegal activities, including the sale of drugs, weapons, and stolen data. The deep web is made up of content that search engines such as Google do not index. Such data includes medical records, financial information, research papers, private forums and networks, and other content. In this case, two familiar people communicate with each other directly over the internet.
Indicators Of Compromise In Threat Intelligence

But it also contains other news and religious sites, private discussion forums, and medical records. You can also find email messages, online bank statements, and much more information on the deep web – information that is usually private and inaccessible by the public on the surface web. So, sites that contain a domain extension like .com, .org, .net, .biz, .info, etc. can be found on the surface web. In addition, the content on the pages don’t need any special or custom configuration to access. As I’ve mentioned, the dark web isn’t just a place of eternal torment, teeming with drug dealers, human traffickers, and a hitman.
In the summer of 2017, a team of cyber cops from three countries successfully shut down AlphaBay, the dark web’s largest source of contraband, sending shudders throughout the network. As long as there’s a demand for the ability to privately browse the internet and, more importantly, host websites anonymously, the deep web will exist. Due to its decentralized structure, there is no real way to “shut down” the deep net, just like you can’t really shut down the regular internet.
Now that you’ve completed the download, it’s time to install the Tor browser on your device. (The installation instructions that follow are for the macOS platform, I’ll mention where it’s different for Windows.) Simply double-click the downloaded file in your download folder. Then, simply click the operating system that you are using and download the file. While an iOS version of the official Tor browser is not available, there are Tor-compatible browsers available in the App Store. But again, your ISP won’t be able to see any of the content you’re reading or what you are sending and receiving through the Tor network. Especially for these people, the dark web is the perfect platform to communicate and publish information without having to worry about imprisonment or any other form of retribution.
- Sites on the surface web (or open web) are those visible to average users without the use of Tor or any other special browsers or software.
- Just because a page cannot be accessed by search engines doesn’t mean it’s trying to promote illicit activity.
- Next, select a dark web search engine like DuckDuckGo that can help you find dark web websites that cannot be indexed by traditional surface web search engines, such as Google or Bing.
- For instance, your email inbox, online banking account, or a company’s internal database resides in the deep web.
- Unlike the surface and deep web, you can’t access the dark web via a standard or specialized search engine.
- You may suspect that it’s a place (or places) where malicious hackers roam.
It might seem a bit scary but the darknet is very useful too, for which it was created, to provide anonymity to the government official, journalists, and even us. But, not everything is illegal on the dark web, there are numerous active secret communities that use this channel as a method of establishing communications and are used by many different agencies. Despite all the dangers, there are actually advantages to using the dark web. It’s a way to access a more open internet since the dark web is decentralized. You’d also enjoy anonymity and privacy thanks to Tor’s encryption and routing, something you don’t get from most normal browsers. But, of course, exercise caution and stay away from anything illegal.
The internet is the network infrastructure we use to communicate globally. You can also include Internet Protocol as a defining feature of the internet. It’s the language of the internet and describes exactly how information is encoded and routed over the internet. If you liked this article, follow us on LinkedIn, Twitter, Facebook, and Youtube, for more cybersecurity news and topics. It consists of a bunch of conservative intellectuals, who traditionally were the only ones allowed to speak in public, aka they were the most visible on traditional information dissemination hubs. Mostly they are the WASP elite middle-aged or older, which weighed in as experts on television shows, published editorials in the biggest newspapers or taught at the biggest universities.
Risks Of The Dark Web
Although most of this Deep Web can contain legitimate content that users can control with privacy settings and requests, much of the Dark Web contains data without the owners’ consent. People worrying about their data need to check their digital footprint periodically and seek services specifically offering data removal and monitoring services in order to minimize the potential risks. Browsing the Deep Web may be safe if users exercise precaution in accessing the web. Therefore, to avoid trouble, make sure that you visit just reputable sites, apply secure connections, and adhere to a privacy directive. Possibilities of exposure to dangers like leakage of data or content violating the law are reduced, providing that the applicable users have the correct credentials and authorization. The surface web, what most users think of as “the internet,” represents only about 10% of total internet content.