Security researchers have been monitoring forums within the cybercriminal underworld to investigate the leading markets operating in 2024. There’s also a privacy angle—some users live in countries with censorship or surveillance, and the dark web gives them a space to communicate or access information more freely. Others are looking for stolen data, hacking services, or even banned books and political content. For sellers, it’s often about making money while staying off the radar.
Search With Language Navigator
In conclusion, the Deep Web is a vast and complex realm that offers both opportunities and risks. It is crucial to understand the distinction between the Deep Web and the surface web, as well as the nuances of the Dark Web. While safety concerns and criticism surround the Deep Web, it is essential to recognize its potential benefits, particularly in terms of privacy and access to knowledge. By following the tips for safe exploration and being aware of the common misconceptions, individuals can navigate the Deep Web responsibly and make the most of its hidden treasures. Remember, knowledge is power, but with power comes responsibility. One of the golden rules of navigating the Deep Web safely is to refrain from sharing personal information.
The Dark Web: Is It Worth The Risk?
Websites claiming to traffic in human beings and offering hitman services are abundant, but there is scant evidence that they are real. “Some Canadians are being drawn into malicious cyber activity, lured by the potential for easy money and social recognition among their peers. This case shows that anonymity is not absolute online and there are real-world consequences when engaging in these activities. The hidden wiki is an encyclopedia like Wikipedia, which is in the deep web, is one of the most complete guides to access the pages with onion links. This virtual bookstore is one of the oldest search engines on the internet. It was created by “Tim Berners-Lee”, who was also the creator of HTML and the Web itself.
Tips For Safe Access To The Dark Web

Though the dark web may not be the monster it’s often made out to be, its very existence poses a risk to the rest of the World Wide Web. Organizations constantly face the risk of data breaches, but the existence of the dark web amplifies this risk. For instance, if a company suffers a quiet data breach, its users’ personal information will likely end up for sale on a dark web marketplace.
The system is designed to provide enhanced security and privacy features. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. Some markets even sell privacy tools, but you are more likely to run across counterfeit prescription pills and stolen identities.
In an onion network, messages are encased in layers of encryption, much like the layers of an onion. The encrypted data is sent through a series of network-based nodes called onion routers. A Canadian market established in 2021, WTN offers over 9,000 products, including narcotics, fake goods, and digital services. It operates in both French and English and has built a reputation for ease-of-use. Known for its publicity stunt releasing millions of stolen card details for free, BidenCash specializes in credit card fraud and identity theft. This article reveals the top 10 dark web markets dominating in 2025, their unique characteristics, and the critical implications for enterprise cybersecurity.

As a result, it would be difficult to locate you or trace the dark web activity back to you. We also recommend using a virtual private network (VPN) such as NordVPN — the best dark web VPN — to add an extra layer of protection. You can read our NordVPN review for more information, or try it out yourself using the 30-day money-back guarantee. Cybercriminals often leverage the anonymity to leak sensitive information, like stolen credentials, credit card numbers, or company data. Even if you try searching for .onion sites on Google, they won’t appear in the results because these sites are designed to remain hidden for privacy and anonymity. As a result, Torch is often considered one of the leading dark web search engines.
Cybersecurity Workforce Trends In 2025 – Skills Gap, Diversity And SOC Readiness
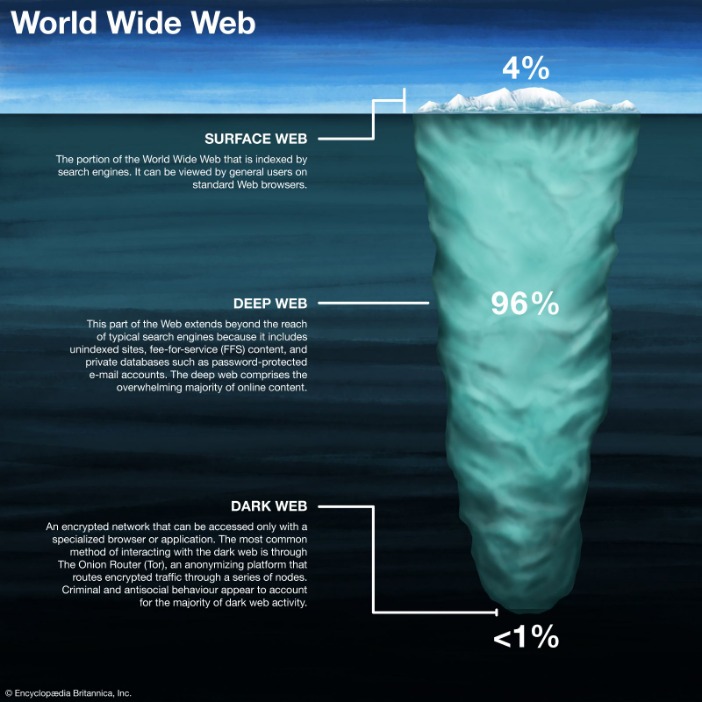
Surprisingly, these password-protected pages make up 90% of the internet1. The dark web, which is considered part of the deep web, isn’t indexed by web browsers, and can only be accessed through anonymizing browsers like Tor. Some tech experts suggest that the dark web makes up for 6% of the internet1.

Directory Of Open Access Journals
Having written about TV shows and series for over 3 years, Ademilade strives to create high-quality content consistently. Ademilade watches his favorite episodes or plays Valorant when not writing. Characters meeting the above requirements are more difficult to brute force, making them safer. If you can’t think of a strong password, consider using a password generator. Google and other companies can also help you generate strong passwords when you sign up on a website and store them in your profile.
- The content in this article is for information purposes only and is not intended to be relied upon as specific professional or expert advice.
- Yippy is a search engine that started in 2009, since then it has evolved.
- A network browser gives you access to sites with the ‘.onion’ registry operator.
- It’s not mysterious or spooky; it’s home to everyday things like scientific research, medical records, private financial information, and secure communications.
- DuckDuckGo is a search engine that prioritizes user privacy, distinguishing itself from competitors by not tracking search history or personal information.
- ChatGPT (openai.com) is a prime example of such an advancementFootnote 13.
The 10 Best Dark Web Browsers In 2025
These sites aren’t just important resources; they’re like lifelines used to serve readers living under oppressive regimes. Some whistleblowers and journalists use these portals to safely leak information, especially when a source requires complete privacy. Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together. Sci-Hub is a massive database that eliminates the barriers to getting scientific knowledge. It contains millions of scientific research documents from around the world. The site seeks to liberate information by making it free to individuals and institutions.
One study found that only 6.7% of Tor anonymity network daily users — a cohort that comprises mostly dark web users — connect to onion sites used for illicit activity. This essentially means that over 93% of Tor daily users use the dark web for legitimate reasons. The hidden web (also known as the deep web or deep net) is the largest part of the internet. It comprises websites that aren’t easily accessible mainly because they are non-indexed, password-protected or paywalled. The dark web is a small subset of the deep web comprising purely non-indexed websites and services. While not strictly a search engine, OnionLinks provides a directory-style resource that helps users discover various .onion sites across different categories.
This layer of security ensures that users can freely express themselves and seek information on sensitive or controversial topics without the risk of reprisal or surveillance. The anonymity offered by Hidden Answers fosters a community where open, honest dialogue can flourish, covering subjects that might be taboo or heavily moderated on conventional platforms. Sci-Hub, often referred to as a “pirate” academic database, is a groundbreaking online repository that provides free access to millions of research papers and academic articles.
Since its launch in 2008, ExpressVPN has helped businesses and individuals stay private and safe online. It works with Tor, Freenet, and Invisible Internet Project (I2P), which form the three major pillars of the dark web. If the antivirus confirms that a file poses any danger to your device, it warns you.
- The major advantage of using a live OS such as Tails is that, on shut down, the OS wipes itself from the thumb drive you’ve installed it.
- However, you cannot simply browse to sites on the dark web — you have to take steps to ensure privacy first.
- If you search for obscure copyright-free ebooks on Google, you’ll have to click through several pages to find a result that provides a download link.
- Accessed through the Tor network, a privacy-focused browser that anonymizes user’s web traffic, The Hidden Wiki operates as a directory service.
The Legality Of Accessing The Dark Web
These sites cater to cybercriminals seeking valuable data, such as credit card numbers, login credentials, and personal information. As of 2020, nearly 57% of the dark web was estimated to contain illegal content, including violence and extremist platforms. However, it is essential to be cautious because it can be a risky place. Moreover, use it only for ethical and legal purposes to avoid legal consequences on the Dark Web. On the other side, the software used to access it, Tor, is not an illegal browser.
The scammers would call these offices, posing as CEOs and managers of the respective corporations, and instruct staff to initiate money transfers into their bank accountsFootnote 34 Footnote 35. Advancements in AI are rapidly improving the realism of deepfakes, as well as making them more difficult to detect and disseminateFootnote 18. Deepfake applications are also becoming more accessible and less technicalFootnote 19. Despite this, there appears to be a lack of awareness or knowledge around deepfakes, and an inability to recognize or detect themFootnote 20. AI has also advanced the speed at which human tasks are accomplished generally. AI-based program AlphaFold, for example, is assessed to have correctly predicted the structures of over 200 million proteinsFootnote 16, greatly advancing research on likelihood and treatment of disease.