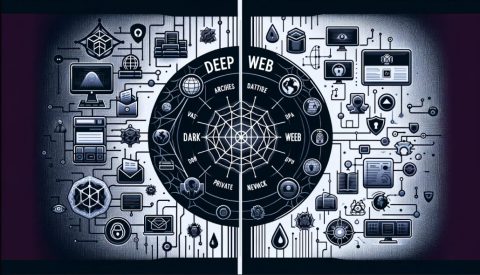
Most of that is legal, like your financial information in banks, social media accounts, email archives, cloud storage, academic journals, streaming libraries, etc. Later, Tor’s underlying code was released under a free license, and a nonprofit called the Tor Project was formed. In 2008, the Tor Browser was released, which made it easy for anyone to get on the darknet. The existence of an anonymous and hidden internet then allowed for alternative information channels and illegal websites to flourish. In 2002, the dark web grew significantly when researchers supported by the US Naval Research Laboratory built and released the Tor network. At the time, the internet was still young, and tracking people was easy while staying anonymous was not.
PRIVACY ALERT: Websites You Visit Can Find Out Who You Are
You can also find websites to download copyrighted material such as music, movies, games, software, and even Netflix credentials. Some downloads contain malware for the fraudsters to hack the unsuspecting user later. Law enforcement agencies don’t pay much attention to the Gray Web, so users don’t feel the need to be anonymous.
Is Using The Tor Network Illegal?
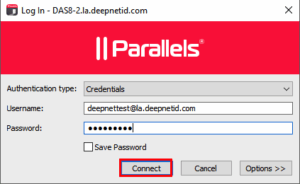
This initiative aimed to protect the privacy of individuals in repressive regimes or those concerned about surveillance, allowing them to read news without exposing their identity. Most deep web websites require login credentials, often with two-factor authentication, and use encryption to protect user information and keep transactions private. If you want to learn all about privacy protection or cryptocurrency, the dark web has plenty to offer. There are a variety of private and encrypted email services, instructions for installing an anonymous operating system and advanced tips for the privacy-conscious.
Why Do People Use The Dark Web?
Please check your local laws to ensure your use of VPN complies with statutory requirements. Always run the latest version of the Tor Browser to protect against security vulnerabilities. Outdated versions may contain weaknesses that attackers can exploit to compromise your anonymity. I recommend enabling automatic updates and checking for new versions before each session. On the other hand, the deep web is that hidden part of the internet, which is personal and open to its respective owners.
#2 Extra Protection
Websites are usually labeled with registry operators like “.com” and “.org” and can be easily located with popular search engines. The dark web comes with its own set of tools and services, including web browsers and search engines (which I’ll get on to in a moment). Part of what makes the dark web the dark web is that you can’t access it through your normal web browser, nor can you look something up on it via a Google search. The dark web, which is what I’m discussing here, is a small subset of the deep web, and refers to websites that are specifically trying to stay out of sight.
If you use the widest definition of the deep web, then it’s a vast ocean of websites. Dark web search engines exist, but even the best are challenged to keep up with the constantly shifting landscape. The experience is reminiscent of searching the web in the late 1990s. Even one of the best search engines, called Grams, returns results that are repetitive and often irrelevant to the query. Link lists like The Hidden Wiki are another option, but even indices also return a frustrating number of timed-out connections and 404 errors. These groups develop their own sophisticated malware, sometimes combined with pre-existing tools, and distribute them through “affiliates”.
A Dark Web Search Engine
- Therefore, it’s a perfectly safe place on the dark web, like many other onion sites you can easily google.
- These operating systems send every outgoing request, not just the web browsing ones, through the Tor protocol, ensuring robust protection.
- To access the Freenet-based dark web, you need to install the Freenet application.
- The average person doesn’t share their private life with just anyone; they let specific people know about it when the information is needed.
- Well-known news websites, such as ProPublica, have launched deep websites.
Sites stored in the index are then ranked based on a variety of different factors, which is what decides how far up on the results page the sites appear in a search. The reason why the deep net provides this level of privacy for website hosts is that the .onion address that you use to access the website obfuscates the actual IP address of the server. This makes it impossible to track down the physical server under ordinary circumstances.
This way, if you’re interested in a specific topic, you can find it quickly. However, Facebook’s dark web version will still log your data, so keep that in mind. While your IP address is hidden, the site can still collect information you share on your profile. Join millions of users who trust ForestVPN for privacy and unrestricted internet access. To stay safe on the dark web, use a reliable VPN, avoid clicking on unfamiliar links, confirm URLs, and never provide personal information. It is also advisable for users to look for phishing scams, where criminals share communications that seemingly originate from a reputable source.

Are Sites On The Dark Web Illegal To Use And Visit?
Another step you can take, which you have complete control over, is to improve the strength of the passwords you use to protect your account. A strong password typically contains uppercase and lowercase letters, numbers, and special symbols and lasts longer than 12 characters. It is one of the most reliable options for streaming or downloading content.
Here’s everything you need to know about this other internet, as well as how to access it. The internet opened the door to a realm of possibilities that permanently changed the business landscape and our personal lives. In a world of bulk data collection, surveillance, and personalized ad tracking, it’s up to us to take control of our personal privacy. We test each product thoroughly and give high marks to only the very best. We are independently owned and the opinions expressed here are our own.
Since you cannot access a library of dark web links using the regular Internet, you can check out platforms dedicated to indexing these sites, like The Hidden Wiki. The deep web is not a series of sites but a storehouse of records, including email accounts, medical records, private messages, and more. Accessing the dark web is legal in itself; the nature of the activities you engage in ensures it stays that way.
VPNs keep you safe in other ways, including preventing IP address leaks and using confirmed no logs that clear your online and browsing data. High-quality VPNs now feature obscure servers for stealth operations and superfast and secure protocols like OpenVPN and WireGuard. Sometimes, people also hide content from the surface web to protect copyright. For example, the Social Science Research Network has over 1 million academic papers uploaded.
DLP Platform
They know how to process the information and get it to the correct law enforcement agencies internationally. We recommend you only visit safe dark web links to explore such as The CIA, Facebook, DuckDuckGo, and Torch. In some countries, evading government restrictions to seek new political ideologies is punishable. For example, China uses the Great Firewall to block access to Western sites. Accessing blocked content can result in being placed on a watch list or imprisonment.
Some hackers offer ransomware as a service (RaaS), where cybercriminals can “rent” a strain of ransomware from its creator in exchange for a fee or a percentage of their ransom payments. Others sell software exploits that other cybercriminals can use to infect victims with malware and steal personal data. The standard dark web browser is Tor Browser, which directs your browser traffic through the Tor network so you can reach the darknet. As your traffic passes through Tor, it’s encrypted and bounced between at least three relay points, known as nodes. This helps obscure the origin of the data (and makes it hard for anyone to find your IP address).
Kurt Baker is the senior director of product marketing for Falcon Intelligence at CrowdStrike. He has over 25 years of experience in senior leadership positions, specializing in emerging software companies. He has expertise in cyber threat intelligence, security analytics, security management and advanced threat protection. Prior to joining CrowdStrike, Baker worked in technical roles at Tripwire and had co-founded startups in markets ranging from enterprise security solutions to mobile devices.