Businesses need monitoring activities in place, but at the same time, they should ensure that the monitoring complies with and adheres to all laws and regulations for implementing dark web monitoring. Some of the regulatory compliance measures include cyber best practices and data protection laws to ensure that monitoring is carried out for ethical as well as threat intelligence only. There’s more to it than just sharing things such as hacked databases, stolen credentials, exploits, or hacking tools. Moreover, they’re home to hot-red forum rivalries, frequent doxxing attempts, and in-depth dark web discussions among other threat actors.
Patterns recommended to avoid include hiring hitmen like Dread Pirate Roberts, and sharing handles for software questions on sites like Stack Exchange. Silk Road quickly grew into the largest darknet market, handling hundreds of millions in transactions. But in 2013, law enforcement traced Bitcoin activity, monitored DPR’s forum posts, and exploited server vulnerabilities to identify Ross Ulbricht. He was arrested in a San Francisco library while logged in as site admin.
How To Hide IP Address In 2025 (A Comprehensive Guide)
All of this has made it one of the most reliable markets still active in 2025. In 2025, the landscape of darknet markets continues to evolve, offering users enhanced security and reliability for drug trade. These platforms leverage advanced encryption technologies and decentralized systems to ensure transactions remain private and secure. The integration of cryptocurrencies like Bitcoin and Monero further strengthens the anonymity of buyers and sellers, making it nearly impossible to trace financial activities.
In the current digital era, where cybercrimes are constantly rising, individuals and businesses need to up their protection techniques. One of the best ways to ensure proper online security is to implement dark web monitoring. Security professionals monitor the dark web forums not only for real-time threat updates and signals, but also as a direct contact with how the cybercriminals operate and think. It’s known that the best place to purchase or even exchange various hacking tools is on the dark web discussion boards. In these forums, you can get stuff like malware, hacking tools, and exploits. They’re the tools that enable cybercriminals to conduct their attacks on businesses, institutions, and individuals.
How Can I Enhance My Privacy While Accessing The Dark Web?
Cryptocurrencies, while offering enhanced privacy, also present significant risks. Users face vulnerabilities like market volatility, scams involving fake escrow services, compromised wallets, or theft through phishing schemes targeting crypto transactions. Furthermore, inexperienced users unfamiliar with secure cryptocurrency practices are particularly susceptible to these threats, risking the loss of their entire funds. CryptBB focuses on the exchange of advanced hacking tools, stolen identity logs, and various exploitation techniques.
Common Scams On Dark Web Marketplaces
Besides, it has a huge and highly active user community that discusses credential lists, hacking tools, email and password combos, vulnerable software, and several other things. It’s so well managed that the platform is multilingual as it features up to 12 language-specific sections, with the French sub-forum being the most active. Best Hack Forum (BHF) is a Russian forum that’s been operational for several years and accessible through Tor and the surface web. It’s a hotspot for cybercriminals as it covers almost everything about illicit activities.
Illegal Pornography
- According to the United Nations Office on Drugs and Crime (UNODC), all guns are manufactured legally.
- The combination of technological advancements and user-centric features positions these platforms as the leading choices for secure and reliable drug trade in 2025.
- The best way to find out is to check the “Have I Been Pwned” (HIBP) website.
- For these reasons, most of these stores naturally like the dark web due to its protection.
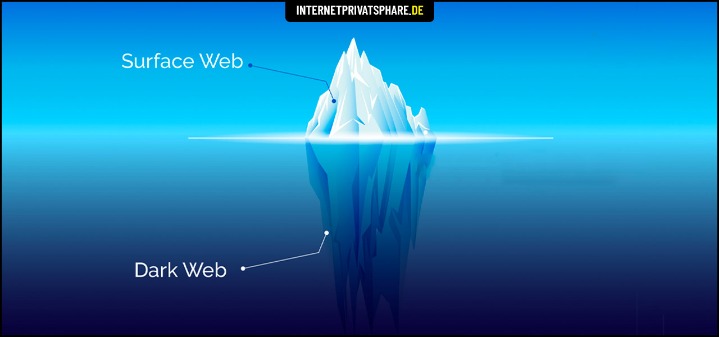
- The dark web, an even more puzzling sublayer, exists within this hidden world.
The forum doesn’t have a mass recruitment structure or flashy marketing, but it’s still a prominent player that needs to be monitored for general users’ safety online. Therefore, it’s one of the most-visited sources of information for both future and past ransomware attacks. It’s also a resource for future and past attackers, which makes it a hotspot not only for cybercriminals but cybersecurity researchers, too.

What Are Onion Sites And How Do I Access Them?
These attacks usually involve DDOSing (overloading) the service and demanding a crypto payment from the site admins to stop the attack. The dark web is a small segment of the deep web, which encompasses all parts of the internet not indexed by standard search engines like Google. Accessing it requires special software, such as the Tor browser, which provides anonymity by routing your connection through multiple servers. Background research tasks included learning from past drug lords, researching legal matters, studying law enforcement agency tactics and obtaining legal representation.

Never Use Your Credit And Debit Card For Purchases
While pressed pills are often made with vitamins, it’s impossible to know that the additives are safe. Note that loading sites with TOR usually takes considerably longer than on the clearnet. It may take anywhere from 15 seconds to several minutes for a page to load, depending on network and site demand. This highly popular English-language market sold all varieties of narcotics. Many of these markets operate internationally, and some have certain specialties. To avoid immediate shutdown, the servers hosting DNMs must be in countries with lax legal regulations.
Typical Use-Cases Of Dark-Web Marketplaces In 2025

Users need a specialized browser like Tor to access these forums, which provides anonymity and encryption to its users. One of the key features of top-tier darknet markets is their use of Tor networks, which provide users with a high level of anonymity. By routing traffic through multiple nodes, Tor ensures that IP addresses are concealed, reducing the risk of exposure.

After all, it’s much less popular, can’t be used to access normal websites, and isn’t as easy to use, among other disadvantages. Both rely on a peer-to-peer routing structure and layered encryption to make browsing private and anonymous. It makes up about 6% of the internet, and it’s where you find everything from illegal marketplaces to forums for whistleblowers. The most recent example is the shutdown of the oldest marketplace Hydra Market in 2022 which took a combined effort of the FBI and the German authorities.
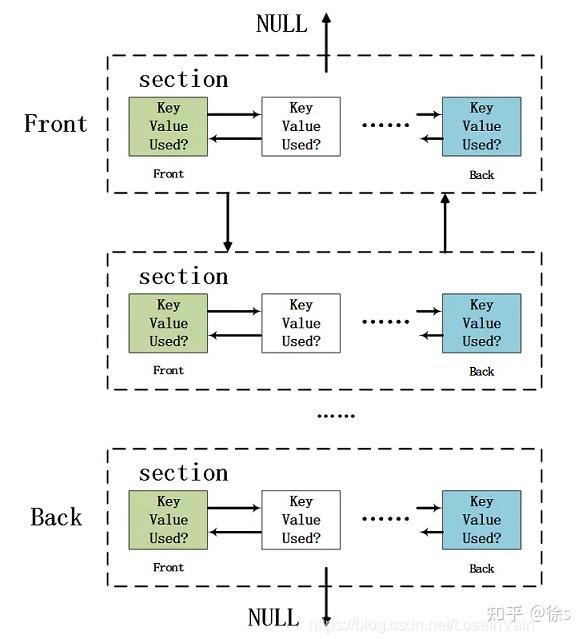
Researchers from the Electronic Frontier Foundation and other groups continued its development and launched the Tor project in 2006 as a tool for journalists, activists, and whistleblowers. Alternatively, users can connect in opennet mode, which automatically assigns peers on the network. Unlike darknet mode, opennet uses a handful of centralized servers in addition to the decentralized peer-to-peer network.
- H25.io is a premium directory in the Tor network, offering access to a diverse and meticulously curated list of onion sites.
- Did you know that Google only shows you a glimpse of all the websites that actually exist?
- As stated above, we don’t condone any activity—on the dark net or otherwise—that is forbidden by law.
- So, even though it does exist on the internet, Google doesn’t index any of these pages or content.
It can only be used to access hidden services specific to the I2P network. I2P cannot be used to access .onion sites because it is a completely separate network from Tor. Instead, I2P uses its own brand of hidden sites called “eepsites”. A handful of dark web search engines that do index .onion sites include NotEvil, Ahmia, Candle, and Torch. The market has built trust among users as it brings vendor reviews from different places and then verifies them with PGP signatures – that way, the buyers feel confident.



