Additionally, Tor exit nodes are often blocked by websites that don’t trust them, and Tor over VPN can’t do anything about that, either. A VPN protects your connection against everyone, not just your ISP and the authorities. It encrypts your connection to prevent outsiders from being able to read your data and masks your IP address with one from a VPN server—so whoever’s looking can’t get any useful information. This process also prevents your ISP from seeing your data or where it’s going. Since the ISP can’t detect you’re accessing dark web URLs, it won’t trigger any alarms about your online activity. You can’t access these .onion sites from your normal web browser like the one you’re probably viewing this page on.
Subscribe To The Blog Newsletter
Use cryptocurrency to buy anything, and use a disposable email address for any type of communication on the dark web. On top of that, the installation process of Freenet is rather easy. Simply download the file, install the software, and you’re ready to use its web-based interface. I2P can only be used to access hidden sites that are only available on the I2P network.
Darknets and dark markets have propelled the growth of cybercrime by offering a platform for the sale and exchange of malicious tools and services. Cybercriminals use these platforms to traffic in stolen data, execute targeted ransomware attacks, and collaborate on advanced hacking techniques. Nation-state actors, too, leverage darknets for espionage and cyber warfare, capitalizing on the obscurity and untraceability they provide. A dark web search engine like DuckDuckGo offers impressive anonymity features and makes it easy to access the shops. These search engines neither track your search queries nor record any information, improving digital privacy and keeping your data private. Its intuitive interface and advanced search features make it easy to find local and global products.
Best VPNs For The Dark Web In 2025
The homepage includes options like browsing products, searching, mixer, and coin exchange. You need to register first to purchase products from this marketplace. All purchases through this marketplace must be made through escrow.
OSINT professionals use the dark web to gather intelligence from hidden forums, marketplaces, and databases that provide early indicators of cyber threats and leaks. This blog introduces the top 21 dark web resources used by OSINT investigators, cybersecurity analysts, and digital forensics experts. Whether you’re tracking data breaches, uncovering financial fraud, or identifying threat actors, these resources will help enhance your dark web investigation capabilities. Background research tasks included learning from past drug lords, researching legal matters, studying law enforcement agency tactics and obtaining legal representation. Patterns recommended to avoid include hiring hitmen like Dread Pirate Roberts, and sharing handles for software questions on sites like Stack Exchange.
Do I Need A VPN If I Use Tor?
The Silk Road was the first popular DNM which appeared on the scene in back in 2011. Many other DNMs have sprung up since selling drugs, stolen merchandise, stolen information, and more. In repressive regimes, darknets play a vital role in enabling free speech and access to uncensored information.
ASAP Market (Best For Drug-Free Listings)
However, it’s much harder to get at the people who are doing the uploading and downloading. However, there are plenty of legal and legitimate online activities that require privacy and anonymity. The dark web is used by journalists, whistleblowers, and political activists who need the protections that it offers. Anything you need to do that has to be off the books to some extent, for noble or ignoble reasons, can be done on the dark web.
- These “credential dumps” allow criminals to access online accounts, steal identities, and commit fraud.
- The Ahmia search engine also has a strict policy against “abuse material,” focusing on users’ protection from potentially dangerous content and malicious attacks.
- While pressed pills are often made with vitamins, it’s impossible to know that the additives are safe.
- Countries differ in how aggressively they monitor Dark Web activity.
- Knowing how to spot a legitimate dark web marketplace can help protect your privacy and funds.
Top Darknet Markets 2025
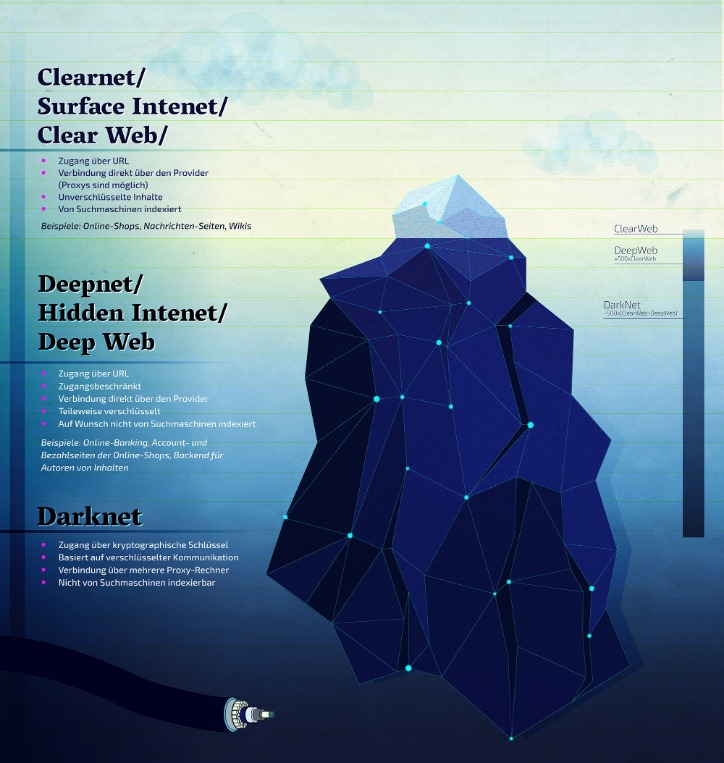
The concept of darknets emerged as a response to concerns about digital privacy and government surveillance. One of the most well-known technologies enabling darknets is the Tor network, which was developed by the U.S. Naval Research Laboratory in the mid-1990s and later released to the public.

Method II – VPN Over Tor
By following these precautions, you can explore the dark web with a greater degree of safety and security. The Not Evil is relatively safe, as it doesn’t track users; however, it doesn’t filter malicious content, so caution is still needed. Although reported as active, there is limited information on Not Evil’s current status, so availability may vary. More often than not, law enforcement is targeting the sellers more than the buyers. Still, it isn’t unheard of for people to be arrested for buying drugs on DNMs. Just because the seller has good reviews does not mean you can trust them.
Where To Find Darknet Market Links

The dark web isn’t indexed by regular search engines and is known as a hotbed of criminal activity. While that’s sometimes true, it can also be used for ethical purposes. There are a lot of misconceptions about the dark web online and in popular media.
This article lists some of the best dark web websites you can visit securely. Some of these sites are very helpful (but unseen as Google doesn’t show them), while others are just for fun. If you make use of a password manager, then it may come with a feature that monitors the dark web for mentions of your email address and password, or any other personal details.
It uses the Tor network because it is a popular network that helps to circumvent censorship and online surveillance. Don’t ever reveal your true identity on the dark web marketplaces because there’s a high chance of hackers and scammers misusing it. Beware of sharing your financial details on the dark web, as this can result in identity theft and your bank account amount being stolen.
Why Is It Critical To Monitor Dark Web Marketplaces?

In fact, WeTheNorth is more of a private club than an open market – something its operators want. The darknet markets are a hotbed for selling stolen personal information. The stolen data can be just anything from full names, credit card details, passwords to social media accounts, bank account information, and social security details, among others. There are some things that you can’t find on the surface internet but are available in the darknet markets.
In some countries, such as China and North Korea, the government uses heavy online censorship and blocks many dark web websites. For example, the BBC website is not accessible in such countries. This is where an Onion website, like the Tor browser, comes in handy. The social media giant is also aware of the many attempts by repressive regimes to restrict its access. After all, it enables users to connect and communicate with each other from around the world. Sections of the dark web are often closed down too, as part of police operations.