STYX market features a robust verification process, making it look more exclusive. The platform supports Monero (XMR), Bitcoin (BTC), and several others to hide identities. The fact that there are no real regulations as well as authorities to monitor transactions, you’re always on your own, and you’re a potential target and victim of a scam or fraud. Perhaps, the figures can tell you what your personal information is worth when it lands on the dark web.
Market operators also know the importance of security mechanisms, and often build their infrastructure with security at its core. Previous studies have mainly focused on social aspects, including analysis of products sold, emerging criminal patterns, criminal ecosystems, and key actors 14, 19, 20, 23, 24, 34. However, the security mechanisms used by the dark web markets have not been addressed in enough depth.
Initially, we tried to use an existing crawler to obtain (sales-related) data for all markets. However, we encountered some difficulties, which also shows the dynamic nature of most market security mechanisms. While dealing with these issues, we were able to jot down the security mechanisms we encountered and run some small experiments against them using the crawler. Chainalysis data shows darknet marketplace revenue dropped post-Hydra seizure in 2022 but recovered to $2 billion in Bitcoin inflows during 2024 Darknet market BTC inflow drop and shift to Monero.
The Increasing Risk Of Data Breaches
In many countries, strict laws limit who can legally buy, own, or carry firearms. So when someone like a private buyer or criminal group can’t pass the background checks or get the right permits, they usually turn to the dark web to sidestep the rules and get armed without drawing attention. The UNODC (United Nations Office on Drugs and Crime) maintains that almost all firearms are originally manufactured through legal means.
Typical Use-Cases Of Dark-Web Marketplaces In 2025
In this article, you’ll find detailed overviews of the top ten Dark-Web marketplaces currently dominating the hidden internet landscape in 2025. We’ll explore their unique features, common use-cases—both legitimate and illicit—and the significant risks users face when interacting with these platforms. However enticing these offerings may be, it’s important to remember that engaging in illegal activities comes with its fair share of risks. Law enforcement agencies are actively monitoring these platforms and taking action against those involved. So tread carefully as you navigate this dangerous landscape and consider the consequences before venturing into the depths of darknet markets. With encrypted messages and cryptocurrencies as payment methods, users can feel secure in their transactions while remaining untraceable.
Anonymity And Privacy Concerns
These marketplaces facilitate the exchange of everything from stolen credentials and drugs to weapons and hacking tools. The anonymity and encryption provided in dark markets create a haven for cybercriminals and nation-state actors to buy and sell dangerous assets while evading detection. The cryptomarket Evolution observed two notable changes in user and post activity.
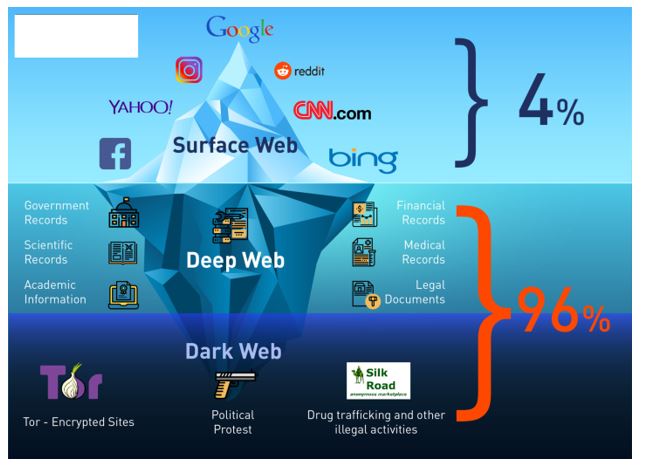
The first thing on the minds of many users when it comes to the dark web environment is illegal drugs. In fact, the Guardian referred to darknet markets as “the eBay of drug dealing,” and rightly so, illegal drugs are found in almost all the shops on the dark web. Nevertheless, most of the items in the darknet markets are illegal or heavily regulated. In fact, according to a study that was done in 2020, over 57% of the websites found on the Tor network contained illegal content. We understand the curiosity to venture into the dark web, but you also need to understand that it’s never safe to venture into this portion of the internet without fully understanding what it entails.
In other words, where degree was a measure of how well someone is connected locally, closeness is a measure of how well connected a node is globally, i.e., to the entire network. RaaS seems to be a small market within the darknet, and vendors are quite resilient in the face of numerous takedowns. Finally, regarding the RaaS target market, the authors found that, based on the items description, most of the RaaS available were targeted to experts while a little bit more than a third were accessible to novices. Moreover, popular items tended to include links to detailed guides and tutorial videos with step-by-step instructions.
AI Vs Hackers How Indian Startups Are Using Artificial Intelligence
To secure against these risks, organizations invest in robust cybersecurity strategies, conduct regular security assessments, and educate employees to recognize and mitigate threats. The interpretation of distance more than a single edge away, i.e., a path, with respect to vendor success in cryptomarket communication networks is not straightforward. After all, other than having a shared author for one of the involved posts, the posts that were responsible for the formation of subsequent links in a path may be wholly unrelated to each other.

Metaplanet Adds $117 Million Bitcoin Purchase, Joins FTSE Japan Index

“So when you see people actually accepting cryptocurrency payments, Monero is really high up there.” “Monero takes privacy seriously. Monero needs to be able to protect users in a court of law and, in extreme cases, from the death penalty,” the site reads. Perhaps because of this, some major cryptocurrency exchanges like Coinbase do not offer Monero transactions. Meanwhile, U.S. regulators have taken notice of difficult-to-track cryptocurrency like Monero, putting the privacy coin in a precarious position.

There are promising signs that we will soon be able to use a collection of scripts that can universally solve the kind of CAPTCHAs encountered in dark markets, which will be a very useful breakthrough. It is envisaged that machine learning techniques can be used to solve them quite easily in the near future. We are only able to cover the end-user side of security mechanisms, which may not be comprehensive. But we also raise ethical considerations for academics on how to properly and ethically improve research in this area.
- Chainalysis data shows darknet marketplace revenue dropped post-Hydra seizure in 2022 but recovered to $2 billion in Bitcoin inflows during 2024 Darknet market BTC inflow drop and shift to Monero.
- These days, it lists over 11,600 illegal items, including hard drugs, hacking tools, and all kinds of cybercrime services.
- In doing so, the FBI was able to obtain information about 59,000 individual user accounts, a senior Justice Department official said during the briefing.
- This interpretation would not be dissimilar to that of the ‘friendship’ relation in a social media network such as Facebook.
- In this system, cryptocurrency is held by a trusted third party until the buyer receives the product or service as described.
How Do Sellers On Darknet Markets Ensure The Security And Anonymity Of Their Transactions?
They really don’t care about the loss and dilemma of the victims whose data has been stolen. For example, an insider or factory employee might quietly slip away with an unmarked gun and sell it online. Once it lands on a darknet marketplace, it becomes part of the illegal weapons trade.
Here, an exponentially decaying weighting function is intended to model the probability of the edge representing a direct response. Chainalysis cautioned that surviving marketplaces are still making massive profits. With over $1.5 billion in revenue generated so far, darknet markets have already recorded a record-setting 2020. According to crypto tracing firm Chainalysis, darknet marketplaces are suffering their largest consolidation in at least five years. “Are they going to pursue all of these marketplaces and continue to do so as new ones emerge?
The ability to seamlessly communicate with vendors via secure messaging systems also greatly improves overall user experience. If you’re using a browser like Tor and visiting .onion websites that aren’t accessible through regular search engines or browsers, you’re likely on the dark web. These sites often look basic or outdated, and their URLs are lengthy strings of random letters and numbers. Keep in mind that visiting the dark web isn’t illegal, but engaging in criminal activity there is. And, of course, think twice before sharing too much personal details online.
How AI Helps In Detecting Stolen Data On The Darknet

AI will advance in predictive intelligence, blockchain tracking, deepfake detection, and AI-driven cybersecurity automation. Yes, AI reduces response times by providing instant threat detection, automated alerts, and actionable intelligence to security teams. AI can monitor employee behavior, unusual access patterns, and leaked company credentials to detect insider threats. Deep learning enhances pattern recognition, behavior tracking, and anomaly detection, improving AI’s ability to analyze complex cyber threats. AI cross-references darknet data with known breach databases, password dumps, and transaction logs to verify if data is stolen. AI can analyze transaction patterns, behavior, and linguistic traits to identify darknet users, but complete de-anonymization remains challenging.