Tor Metrics is a set of tools and data provided by the Tor Project that offers insights into the performance, usage, and activity of the Tor ecosystem and its nodes. Besides monitoring and improving the network, the data can be used to detect possible censorship or attacks. Due to the privacy-forward ethos of the Tor project, Tor Metrics stresses that the data it collects must not undermine the anonymity or security of the network. ProtonMail is a Swiss-based encrypted email service that doesn’t require personal information when you sign up.
The use of the dark web raises suspicion as it shows there is something you want to do privately. Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. The system is designed to provide enhanced security and privacy features. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity.
- But unlike other wallets, you don’t have to worry about your personal information being leaked since it’s hosted on the Tor network.
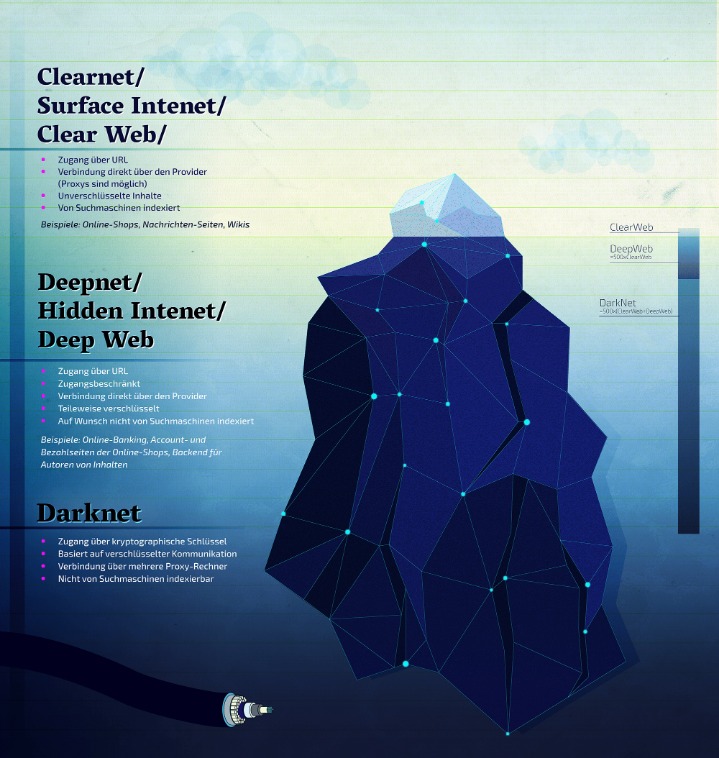
- The surface web is the open part of the internet, which includes publicly accessible websites and resources.
- Rule No.41 allows a federal judge to issue a search and seize warrant for any person who is using anonymity software like Tor.
- Most likely, the native account on your device has full admin permissions by default.
- DuckDuckGo is a helpful search engine available on the Tor that allows you to browse the dark and regular web anonymously.
Archetyp Market Stands Out For Its Commitment To User Privacy And A Diverse Product Range
Encrypted communication channels on the dark web allow users to message back and forth in an anonymous online environment. However, some surface web platforms like ProtonMail offer encrypted email services in addition to dark web versions that enable people residing in more repressive areas to communicate freely. These search engines catalog .onion domains, which are not easily accessible from regular web browsers. These top 10 dark web search engines are important for research, evidence collection, finding hidden resources, intelligence, and various other resources that are not easily accessible. Still, even with these crackdowns and better defenses, dark web markets just keep coming back.

Operating through Tor, DuckDuckGo provides a non-censored search engine experience without logging personal data. Saheed Aremu passionately advocates for digital privacy and cybersecurity in the modern digital age. As one of PrivacySavvy’s resident VPN experts, he guides readers on protecting their online information and anonymity. Saheed earned his degree in Technology and Ethics from the University of Lagos in Nigeria. Since then, he has dedicated his career to writing extensively about crucial infosec, data privacy, and cybersecurity topics. When he’s not empowering PrivacySavvy’s readers to take control of their online security, Saheed enjoys distance running, playing chess, and exploring the latest open-source software advancements.
Hidden Services Directories, Hosting, Portals, And Information
Fraud and scams run rampant on the dark web, including offers too good to be true and fake services requiring upfront payment. Hackers sell access to email accounts, social media profiles, or other information that can be used for identity theft. The Hidden Wiki is a surface website offering a collection of dark web links. Before visiting any dark websites, get comprehensive cybersecurity software to help protect yourself from threats you may encounter. The quickest way to access the dark web is to download and install Tor Browser, which will route your traffic through the Tor network and let you access the dark web.

Dark Web Links: The Best Onion And Tor Sites In 2025
Decrypting the data involves peeling back layer upon layer of encryption, hence the “onion” analogy. ProtonMail is an email service that uses end-to-end encryption, making your email accessible to you and only you. The service retains no copies of any data that passes through a ProtonMail account. Although ProtonMail also exists on the clear web, accessing it via Tor provides an extra layer of privacy if you don’t want to leave a trace of you even using ProtonMail. SecureDrop uses Tor to provide a safe way for whistleblowers to contact various news outlets.
Ways Small To Midsize Businesses Can Stay Safe In The Cloud
Local offices frequently monitor suspicious activities that involve their jurisdictions, so authorities might be closer to your anonymous communication than you know. Since most Tor websites are non-indexed and unregulated, the probability of scams is much greater on the dark web. Malicious actors can prey on unsuspecting users without leaving much of a digital footprint on Tor, so it’s often just a matter of time before you run into one. SecureDrop is designed explicitly for journalists trying to preserve the privacy of their sources. Its anonymous nature enables users to create and submit encrypted documents, chat securely, and receive private responses from journalists. Ahmia also discourages access to illegal content and promotes safer internet practices.

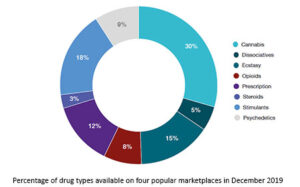
What Do People Sell Or Exchange On Darknet Markets?
This makes it extremely difficult to find out who you are transacting with. This service is a good source of statistics if you have a school project requiring research on Tor and the dark web. However, note that the site only uses non-sensitive and public data for the metrics. The Tor Metrics is a good place to get more information about the Tor project.
Encryption
For example, DuckDuckGo is the most popular but often shows repetitive results and is sometimes unrelated to the question. The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China. It will make your VPN activities seem like normal traffic, so you can use an uncensored internet. However, this feature is only available on iOS, Android, and Windows.
Dark Web Tools And Services
Speak your mind here without fear, as onion links are immune to censorship. Even if you’re using a private, anonymized crypto wallet, there are other ways your identity can be revealed—even if it’s something as simple as letting a personal detail slip in an instant message. It also offers a comprehensive list of marketplaces, exchanges, and websites linked to fraudulent activities, helping you stay informed. The story of dark web marketplaces kicks off with Silk Road, launched in 2011. It was the first big site where people could anonymously buy drugs using Bitcoin, and it gained a lot of attention, until it was shut down by the FBI in 2013. AVG Secure VPN encrypts your internet traffic and obscures your IP address every time you use it to go online — dark web or not.
Without further ado, let’s take a look at some of the best tor and onion links for you to check out, in no particular order. Email is one of the least secure communication systems; the email providers have access to the contents of your inbox. For evidence, look no further than the way Google automatically adds travel information, meetings, and other diary entries onto your calendar.
Using DuckDuckGo over Tor will also let you see onion sites and normal pages in your search results. Swiss based ProtonMail is an encrypted email service that is quite popular with the cryptocurrency community. It’s a paid service, and while it’s extremely secure you will need another email address to sign up, which can leave traces of your true identity without you realizing. Deutsche Welle (DW) is a German state funded news organization that reports on worldwide topics and events.

If you take a quick look through darknet marketplaces, you’ll instantly notice an overwhelming supply of pirated content. We’re talking about even early access to unreleased music, leaked TV episodes, concert footage, and even popular video games before they officially drop. The marketplace supports multiple payment methods, including Bitcoin (BTC), Litecoin (LTC), and Cryptocheck. They add new batches of stolen data every other week, and there’s even a bidding system where buyers can place offers on new data batches as soon as they become available. While this market started in Canada in 2021, WeTheNorth now sells to both Canadian and international users.
You can conduct discussions about current events anonymously on Intel Exchange. There are several whistleblower sites, including a dark web version of Wikileaks. Pirate Bay, a BitTorrent site that law enforcement officials have repeatedly shut down, is alive and well there. By exploring these categories of resources, users can discover that the dark web’s landscape is more nuanced than popular portrayals suggest. Education, activism, journalism, and creativity all find refuge here, protected by layers of anonymity. However, it’s vital to approach each new platform with caution—vetting its authenticity, reputation, and purpose before fully engaging.
It works as a decentralized, peer-to-peer network that emphasizes censorship resistance and complete anonymity. It is a private search engine that lets you search the regular internet via Tor. This allows you not only to visit sites with the added privacy provided by the Tor network, but also search the web as privately as possible from inside the Tor browser. The Dark Web may have a sordid reputation, but there’s plenty of legitimate websites out there for people who just want to browse anonymously.