Additionally, we’ll cover core similarities and key differences between each platform in order to better understand that not all cybercriminal based communities are created equally. In Blackhat Resources channels, users share knowledge about using various hacking tools. Information about tool capabilities, such as ”Free Trial For 30 minutes only for 1 month DM for access,” helps users make informed decisions. This exchange of information supports skill development within the community.In Artificial Boosting channels, education is more informal, focusing on effective engagement tactics.
What You Need To Know About Dark Web Telegram Chat Groups And Channels

Ultimately, it is up to each individual user to decide which platform best meets their needs. Gathering threat intelligence on how cybercriminals operate is one of the most effective ways of ensuring that your security matches the most up-to-date attack techniques. In the evolving world of digital communication, Telegram has increasingly been compared to the dark web due to its growing use for illicit activities. With its emphasis on privacy and encryption, Telegram has attracted a diverse range of users, including those exploiting its features for illegal purposes.
Users ask questions to clarify how to use specific software or resolve issues, much like in Credential Compromise channels. This reflects a need for guidance to effectively use pirated software and troubleshoot any problems that arise. The battle against piracy and the protection of copyright have become pivotal issues in the digital era.
- This accessibility contributes to the platform’s role as a hub for illegal activities, enabling a diverse range of users to engage in covert operations.
- The debate surrounding Durov’s arrest has brought these issues into sharper focus, raising questions about the platform’s commitment to enforcing its policies and addressing the misuse of its features.
- However, no platform is completely immune to threats, and Telegram users should be aware of common threats that can potentially compromise their privacy and security.
- This tool enables users to launch scalable DDoS attacks with minimal technical expertise.
- It is important to remember that cybersecurity is a constant effort that requires your security leaders and end users to stay informed about these threats in order to preserve a safer online environment.
- Using a service like FYEO’s active database—which alerts you when your credentials, passwords, and other data appear online—can help you take quick action when someone steals your personal information.
This use mirrors the dark web’s role in fostering extremist ideologies, providing a secure environment for the spread of harmful content and coordination of criminal activities. Despite having their Telegram channels shut down multiple times for violating platform rules, Dark Storm Team consistently manages to resurface and continue operating. Their resilience demonstrates how cybercriminal groups adapt and evolve, using Telegram as a critical tool for coordinating and executing attacks. There is an active demand for OTP bots, as many of these results displayed activity within minutes of the query.

Detection Vectors And Law Enforcement Response
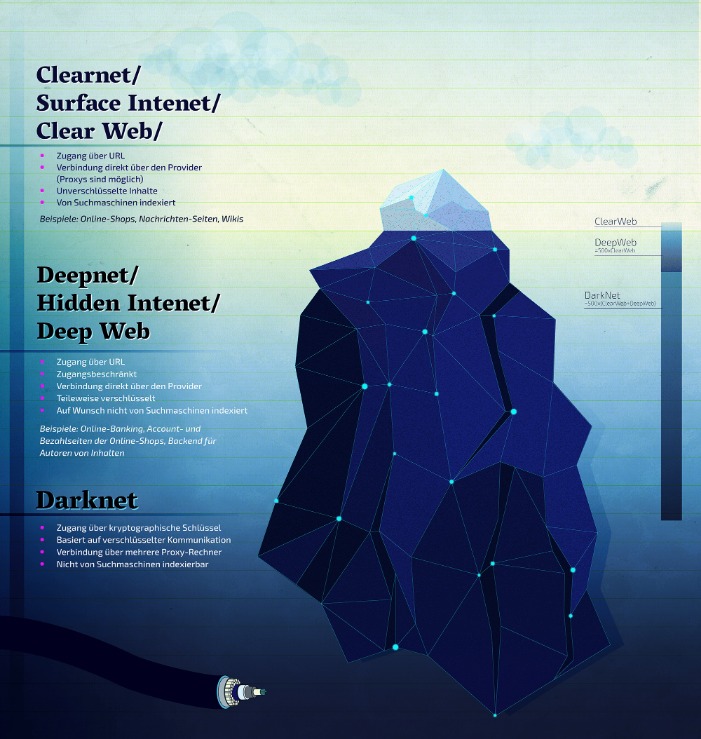
Therefore, dark web users and the dark websites owners are now moving to Telegram, choosing their convenience and leveraging the platform’s anonymity and the ‘secret chat’ feature. On the other hand, Telegram is much more user-friendly and accessible for threat actors to set up an account along with joining or starting their own channel. Most Telegram channels including illicit communities can make criminal activity on the platform more accessible and easier for even low-level cybercrime.
Parallels Between Dark Web Forums & Illicit Telegram Communities
The collapse of Hydra Market in 2022, once responsible for over 80 percent of darknet market traffic and more than $5 billion in lifetime turnover, created a vacuum. When law enforcement seized Hydra’s servers, displaced vendors and customers turned to Telegram. Within weeks, Hydra-branded channels appeared offering drugs, stolen data, and counterfeit documents.
- In Blackhat Resources channels, users share knowledge about using various hacking tools.
- The platform’s design, which emphasises privacy and minimal regulation, has made it a favoured space for extremist groups.
- This scandal alone gave Telegram enough popularity that it saw 25 Million new users signing up on Telegram in just 3 days.
- That might sound cool if you’re sending messages to a loved one, but it also means that third parties can’t access illegal content—or do anything about it.
- These sites act as a network for career cybercriminals to connect with potential collaborators.
Dark Electro (Frozen) Telegram Channel
If you come across a Telegram channel that violates the law, please contact us using the contacts listed in the site menu. After reviewing the complaint, we will remove this Telegram channel from the search. For the search, you can select the category you are interested in or enter your query in the search bar.

Data Leak Monitoring: A Radar For Breaches And Cyberattacks
Leaked data reportedly included sensitive financial information about prominent figures and institutions. While reports don’t mention any financial loss yet, the incident has caused huge reputational damage with the anti-corruption group Transparency Maroc demanding public revelation of those responsible for auditing and managing cybersecurity systems. In June, 2024, the Qilin ransomware group targeted Synnovis, a laboratory services provider for National Health Service (NHS) hospitals in South-East London. Attackers exfiltrated 400 GBs of sensitive information and subsequently leaked it on Telegram after ransom negotiations failed. The breach highlighted vulnerabilities in healthcare supply chains and the misuse of Telegram for data dissemination. Moreover, the attack led to the cancellation of over 1,100 operations and 3,000 outpatient appointments across seven major hospitals, subsequently costing £32.7 million in damages.
Resources
These fraudsters might use social engineering techniques to steal your personal and financial details. Others might trick you into signing up for fake NFTs or a bogus cryptocurrency investment scheme. Sorry to break it to you, but Telegram is so much more than chatting to friends and exchanging cute cat GIFs.

Researchers tracking these groups noted that Telegram’s broadcast and bot features allowed operators to recreate the functionality of darknet forums almost overnight. Law enforcement in Russia and Germany confirmed that Hydra affiliates were using Telegram bots to automate sales, effectively replicating market infrastructure in a mobile app. One of the main objectives of threat actors is to exploit the monetization potential of stolen information. By breaching the security of infected devices, they gain access to valuable data such as browser fingerprints and login credentials.

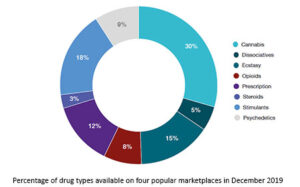
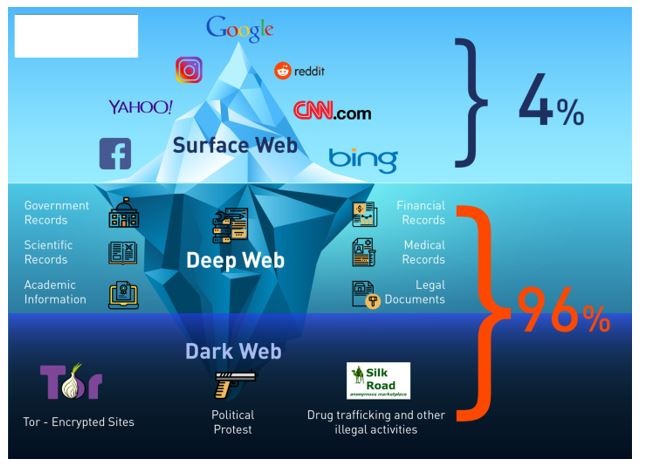
While some may consider the dark web and the deep web to be synonyms, the deep web is actually a much broader web class that makes up the majority of the internet, yet isn’t public-facing (for example, found on most search websites) or indexed. The Darknet Telegram Directory is a curated list of links to various darknet channels and groups available on the Telegram platform. The directory provides a comprehensive collection of darknet-related information and resources for those interested in exploring the hidden aspects of the internet.
Related Content
Even though they can be sold for just a couple of dollars, browser fingerprints and stealer logs can represent the digital lives of their victims. With saved login credentials and more (especially combined with OSINT), a threat actor could even guess the victim’s general geographic location. They distribute stealer logs themselves for free, while monetizing access to the channel through subscriptions. This way, they can have access to fresh stealer logs without waiting for autoshop sales. For example, we found a channel with a $100 per month subscription that promises a minimum of 1,000 new logs per day. “The marketplace can be accessed by simply installing the Telegram app, which can be installed on almost every (modern) mobile phone, the specific marketplaces can then be found using the built-in search function of the Telegram app,” Lummen wrote.
Called Huione Guarantee, it provides scammers with personal data and tools to perpetrate their frauds. “With transactions totaling at least $24 billion, it is the largest illicit online marketplace to have ever operated,” cryptocurrency tracker Elliptic wrote in a report today. Elliptic rival Chainalysis had previously said Huione Guarantee had processed as much as $49 billion. It “dwarfs Hydra, the largest ever darknet market, which received approximately $5 billion in cryptocurrency over its six-year lifespan,” the company added. For organizations to effectively protect themselves from these continuously changing threats, cybersecurity strategies must include monitoring both of these platforms.
In January, state police in Latvia set up a separate unit specialising in monitoring chat apps for drug trafficking and communication, and officials have named Telegram as a particular concern. All the images were posted to the groups, and we have altered the names of the channels so as not to advertise them. I changed my settings to stop it, but now every time I log on I am treated to thousands of new messages across dozens of extremely active illegal groups. “Is Telegram the new Darknet? A comparison of traditional and emerging digital criminal marketplaces.” Master’s thesis, University of Twente, (2023). In addition to sharing leaked records, the channel also offers custom scripts, scammer lists, and discussion groups, where members can exchange information and engage in transactions related to compromised databases. Flare integrates into your security program in 30 minutes and often replaces several SaaS and open source tools.