That’s why client has to enumerate ciphers to be able to find those supported by server and for that to do at least one new start handshake (ClientHello) for each cipher suite. One tool I haven’t seen mentioned in other answers is Stephen Bradshaw’s SSLTest, which, among other things, is intended to compare “the detected ciphers and protocols against compliance standards such as DSD ISM and PCI-DSS.” There is no better or faster way to get a list of available ciphers from a network service. Plus, nmap will provide a strength rating of strong, weak, or unknown for each available cipher. The following is an example of how you can connect to a Neo4j DBMS in read mode and then change the access mode to write in the interactive shell.
Repository Files Navigation
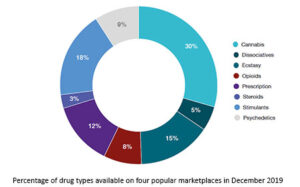
You can send sensitive data through HTTPS connections that it will be encrypted during transport. Just your app and the server will know any parameters sent through https. After a relational dataset has been imported, there may be further labels that can be added, depending on the use case.Additional labels can speed up pinpointing a node if you use them in your queries. Since 2020, 2easy has sold massive stealer logs with sensitive data like passwords, bank cards, and initial access credentials.

It operates in both French and English and has built a reputation for ease-of-use. Launched in 2020, Cypher Marketplace sells fraudulent documents, stolen credit cards, fake IDs, and malware. Its emphasis on user anonymity and document forgery makes it a core tool for identity fraud. Founded in 2014, BriansClub remains one of the oldest and most infamous dark web markets for stolen credit cards, fullz (complete identity kits), and dumps. New, updated, deprecated, and removed features must be recorded on the Deprecations, additions, and compatibility page.
Cypher And SQL: Key Differences
Let’s see how it looks within the TCP packets of cloudflare.comSo, I caught a “client hello” handshake packet from a response of the cloudflare server using Google Chrome as browser & wireshark as packet sniffer. I still can read the hostname in plain text within the Client hello packet as you can see below. Note that when you use a HTTP Proxy, it knows the address (domain) of the target server, but doesn’t know the requested path on this server (i.e. request and response are always encrypted). As the other answers have already pointed out, https “URLs” are indeed encrypted.
- Cypher is well-suited for application development and data analytics.
- Elevate your shopping journey and discover the true potential of our exceptional cypher darknet aggregator.
- Whether you’re in the market for the latest cypher website trends or searching for timeless classics, our marketplace has it all.
- Our marketplace is not just about cypher darknet – it’s about providing you with the best possible shopping experience.
- Neo4j’s query language Cypher supports loading data from CSV directly but not from JSON files or URLs.
Sam Bent’s Post
It is worth noting that Cypher requires buyers to rely on the market to encrypt shipping information, which may be disconcerting to some. Nevertheless, the payment system employed by Cypher is highly efficient and represents an optimal solution for buyers. Our summer camp treasure hunts got so much more exciting with this tool! I create encoded clues that kids have to decode, and they absolutely love it.

Then submit them to the server one by one to test them individually. I am not suggesting that you do this manually; this is a situation in which a little automation goes a long way. In fact, this is a situation in which looking around for a good tool might be appropriate. To find the best solution, we should first answer ‘why do we want to enumerate all supported ciphers? Here the focus is on the security aspect, i.e., to find out if a server is vulnerable or not.
Secret Code Translator Free Decoder & Encoder Tool
Here, concerned link items are encrypted at the server end (through PHP), and Javascript on the client side decrypts them to take appropriate action. The examples in this section use the MATCH (n) RETURN n LIMIT 5 Cypher statement and will return 5 nodes from the database. H25.io is a premium directory in the Tor network, offering access to a diverse and meticulously curated list of onion sites. Our mission is to simplify navigation in the complex and evolving world of the darknet. Here, you’ll find links to various resources, including educational archives, private forums, anonymous services, and more. Generate secure links for recipients to decode messages using the same encryption key.
Removing Properties From A Node

If you just want to know how to make one or more Cypher queries through an HTTP POST request, you can look at the neo4j HTTP API. Connect and share knowledge within a single location that is structured and easy to search. In Cypher, you can depict a node by surrounding it with parentheses, e.g. (node).The parentheses are a representation of the circles that compose the nodes in the visualization.

Cypher Syntax
This query can be rewritten with the DETACH clause to achieve the same result. The WITH clause is used to chain together parts of a query, piping the results from one to be used as a starting point of criteria in the next query. Using OPTIONAL MATCH when returning a relationship that doesn’t exist will return the default value NULL instead. After deployment, verify your contract on Cypherscan to make the source code accessible for public inspection. The RPC URL connects your development environment to the Cypher testnet, while the Gateway URL facilitates encrypted operations, such as decryption or re-encryption, when interacting with Cypher. SSLyze is Python based, and works on Linux/Mac/Windows from command line.
Relationship Types
Be aware that since the filter inside WHERE can contain any kind of an expression, the expression can be so complicated that the index doesn’t get used. If there is any suspicion that an index isn’t used, we recommend writing labels and properties inside the MATCH pattern. You can explicitly create indexes on a data with a specific label or label-property combination using the CREATE INDEX ON syntax. Because the WHERE clause contains the statement c.language IS NULL, the node will only be matched if it doesn’t have a language property. The CREATE clause creates two new nodes and a directed relationship between them.
But if someone is infected with this kind of software, they will have access to the data, no matter what you use to transport it. So, beware of what you can read because this is still not an anonymous connection. A middleware application between the client and the server could log every domain that are requested by a client. Yes, the SSL connection is between the TCP layer and the HTTP layer.
With a decent product range and all the must-have features incorporated (e.g., Escrow/FE, Bitcoin/Monero, 2FA with PGP), it is a great place to shop unless you’re longing for something peculiar. Yet, as the number of participants continues to grow, security features will become pivotal and will definitely call for upgrade or improvement. Essentially, it’s a traditional trading platform with all the mandatory features.
At the heart of our vision for the future of cypher url shopping is a deep commitment to empowering cypher mirror connoisseurs. We recognize that the true value of exceptional cypher url lies in the unique stories, craftsmanship, and personalized experiences that they offer. In a graph model, data is structured as nodes (vertices in math and network science) and relationships (edges in math and network science) to focus on how entities in the data are connected and related to one another. Our cypher link aggregator is constantly evolving, driven by a commitment to innovation and a deep understanding of the ever-changing needs of our customers.