
Multi-signature escrow and real user feedback make it trustworthy. They’ve got a mix of drugs and hacking tools, nothing too wild. For 2025, they’re tweaking the mobile site, which I’ve been wanting forever—makes it easier on the go, especially if you’re using Tor on your phone (see how). It’s not fancy, but it’s dependable, and that’s why I keep coming back. WeTheNorth is a Canadian market established in 2021 that also serves international users. It offers counterfeit documents, financial fraud tools, hacking and malware services.
Plus, we’ve got some fresh takes on dark web trends and how to get started. It has a bidding feature, with new batches of stolen data being frequently added. Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement. There’s also a privacy angle—some users live in countries with censorship or surveillance, and the dark web gives them a space to communicate or access information more freely. Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools. And, of course, think twice before sharing too much personal details online.
Saved Searches

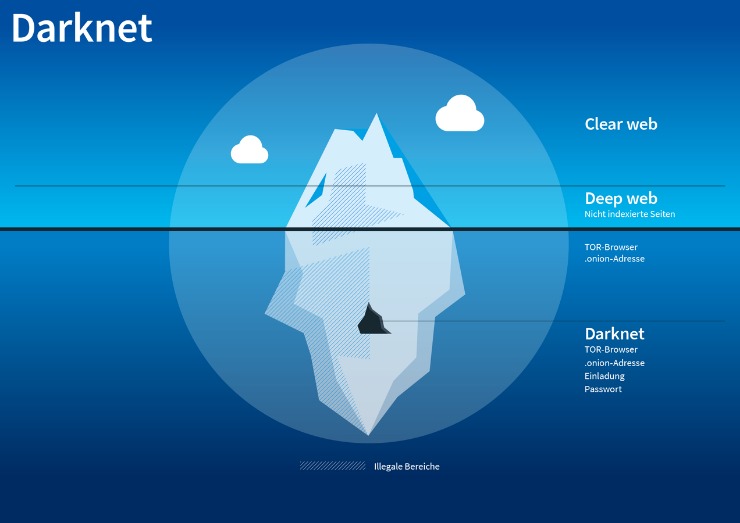
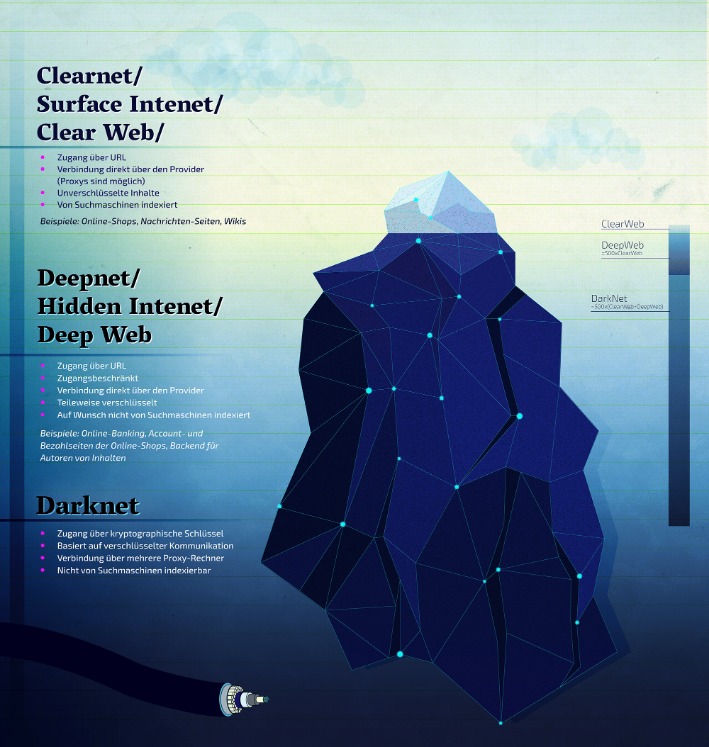
Brian’s Club is one of the best place to buy stolen credit card info, including CVVs, dumps, and even full account packages without revealing your identity. The dark web itself is not illegal, but it’s largely connected with unscrupulous and illegal operations. That’s why it has such a foreboding and even dangerous reputation. It is used by many for buying or selling items that are prohibited on the regular internet, like fake IDs, illegal drugs, and stolen data.
Want to get illegal drugs, fake passports, Trojan, or other cyber attack software? Welcome to this collection of darknet resources, curated exclusively for educational and informational purposes. This repository serves as a knowledge hub for individuals interested in understanding the structure, functionalities, and applications of the darknet. Please note that all material provided here is aimed at promoting awareness, responsible research, and ethical use of information. We provide regularly updated, authenticated Ares URLs to ensure you never fall victim to phishing sites. Ares implements end-to-end encryption for all communications and transactions.
Account Setup And Transaction Testing On Ares
Users favor marketplaces with straightforward navigation, efficient search functions, and clear product categorizations. The ability to seamlessly communicate with vendors via secure messaging systems also greatly improves overall user experience. Ideal marketplaces support anonymous browsing through networks like Tor and I2P, utilize privacy-focused cryptocurrencies such as Monero, and implement measures to prevent tracking and transaction tracing.
Deep Web Forums

While it provides unparalleled privacy, it also harbors potential dangers. With Forest VPN, you can explore this intriguing world safely and securely, ensuring you remain anonymous and protected. So, next time you’re tempted to explore the dark web, remember the importance of staying safe and secure with the right tools at your disposal. Dark Matter is an intricately designed platform, built from scratch with a distinctive and invigorating visual appeal.
How To Protect Your Identity While Browsing The Dark Web
- Despite growing crackdowns from law enforcement agencies, the dark web remains a hotbed of criminal activity, offering everything from drugs to stolen data.
- Its interface is easy to navigate, and it has a reliable escrow system, as well as allowing payments with Bitcoin and Monero.
- This just involves turning on your VPN before you open Tor and connect to dark web sites.
- The site was a pioneer in using Tor and Bitcoin to maintain anonymity.
- All of the darknet markets have .onion domains which can only be accessed using Tor.
Although dark-web marketplaces utilize technologies like Tor and I2P to enhance anonymity, these methods are not foolproof. Law enforcement agencies continuously improve their ability to trace transactions and monitor marketplace activity. Simple mistakes—such as inadequate operational security practices, sharing identifiable details, or using compromised devices—can quickly compromise anonymity and expose users’ real-world identities. Abacus Market has emerged as one of the most reputable and widely used dark-web marketplaces in 2025. Founded in early 2023, shortly after major law enforcement operations shut down several competing platforms, Abacus quickly filled the void by prioritizing reliability, advanced security, and user anonymity. While some of these markets were shuttered by law enforcement agencies – some took the easy way out with exit scams.
Word’s out they’re going decentralized in 2025—less downtime, more trust, right in line with where things are headed. The site’s slick—vendor stats update live, checkout’s a breeze, and the vibe’s modern without being over-the-top. I’ve used it a handful of times; deliveries landed smooth via DeadDrops—plain packaging, no fuss.
How To Access Darknet Market Links ?
- Onion sites (aka Tor sites) are websites only accessible on the dark web; you can’t view them using a regular browser.
- Unfortunately, the dark web hosts not only explicit but also deeply illegal and disturbing content.
- The site’s dead simple to use, and vendors leave feedback that’s actually helpful.
- Those who use these services can still be traced and prosecuted if caught, especially as law enforcement continues to sharpen its tracking tools.
The cybercriminals trade even sensitive documents, such as medical records, passport information, and driver’s licenses. But somewhere between production and purchasing, things can get dirty. For example, an insider or factory employee might quietly slip away with an unmarked gun and sell it online. Once it lands on a darknet marketplace, it becomes part of the illegal weapons trade. As we mentioned earlier, not everything sold on dark web markets is illegal. As terrible as its reputation may be, some vendors sell legitimate goods or services.
Nexus Marketplace
While the support for Monero is a positive aspect, the absence of per order (Direct Pay) or multisig escrow options increases the risk of potential exit scams. Therefore, buyers should exercise some level caution when using this market and only deposit enough funds to cover one order at a time. Torzon Market has been created by a team who evidently have good knowledge about what it takes to make a good darknet marketplace. The interface is clean and user friendly, and there is a good selection of features on offer. So, it’s not an easy question to answer, but there are a number of ways you can approach it and try and tackle that issue. Malicious files can compromise your device with malware or ransomware.
Are Onion Sites Safe?
Additionally, do not attempt to buy anything on the dark web as most transactions are illegal and can lead to scams. Tor Browser, built on Firefox, encrypts your traffic across 3+ relay nodes, enabling access to .onion sites. In 2025, it powers 2.5M+ daily users, with Germany leading in usage (followed by the U.S.). In addition to its emphasis on stolen credentials, 2easy Market offers a variety of cybercrime tools, such as hacking services, exploit kits, and other resources for conducting cyberattacks. Russian Market has consistently remained one of the most popular and valuable data stores on the dark web. Its affordability and reliability have earned it a loyal customer base.
What Exactly Is Sold On These Marketplaces?

This makes it incredibly difficult to find out who you are paying. One of the most popular ways to get around the dark web is not to use a search engine at all. Just like in the old days of the internet, the dark web maintains numerous indexes of sites, like The Hidden Wiki.
The victims, who are common users, businesses, and even banks, who end up paying the price. These hackers don’t hide in the shadows as much as you might think. In fact, many openly advertise their services on darknet forums. Anything from planting malware and stealing sensitive files to hijacking email accounts or breaking into social media profiles.



