Buyers would pay in Bitcoin, hoping to receive counterfeit bills that could pass as real. However, many were left empty-handed or received poorly made counterfeits that were easily detectable. These scams not only resulted in financial loss but also carried significant legal risks, as attempting to use counterfeit currency is a serious crime. In the end, the scammers themselves often became victims of their own fraudulent schemes. Counterfeit money refers to imitation currency produced without the legal sanction of a government, typically with the intention to deceive or defraud. While counterfeiting has existed for centuries, the digital age has made the tools and resources counterfeit money sale online needed to produce fake currency more accessible than ever before.
A Quick Guide On How To Use A VPN With Tor
- He described it, in his thesis for Edinburgh University titled ‘A Distributed Decentralised Information Storage and Retrieval System,’ as a network to allow people to communicate freely without being tracked.
- If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic.
- You should never use your personal information on the dark web anywhere else in your life.
- This is another money-spinner for illegal investors to make a quick profit.
- And then along came the Flashpoint analysts who found even bigger illicit “bargains” in these dark web marketplaces.
These interactions help law enforcement track the identities and operational tactics of criminal organizations. The dark web provides a platform for criminals to conduct illegal financial transactions, such as money laundering. It offers a level of anonymity that makes it difficult for law enforcement to track and trace these transactions.
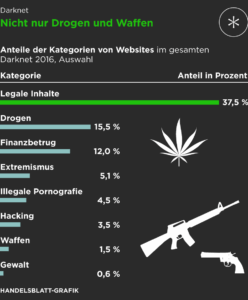
The buyer, meanwhile, has to move out of the shadows to profit from their purchases. The risk of getting caught and the considerable legal consequences this brings makes these dark web sites a buyer’s market, hence the low pricing. Even if you’ve never visited these markets, your personal and financial data might already be there, having been leaked through a data breach. Criminals use this information for money laundering, opening bank accounts, applying for loans, and draining your finances. Many listings involve stolen personal information, including credit card data, Social Security details, and full identity profiles. Most of the remaining categories contribute only a little, with most representing only 2% or less of all counterfeits.
Counterfeit Goods & Services

H25.io is a premium directory in the Tor network, offering access to a diverse and meticulously curated list of onion sites. Our mission is to simplify navigation in the complex and evolving world of the darknet. Here, you’ll find links to various resources, including educational archives, private forums, anonymous services, and more. The successful takedown of Wall Street Market in 2019 involved simultaneous operations coordinated by law enforcement agencies in Germany, the Netherlands, and the United States.
Biggest Dark Web Marketplaces
This post concerns a vendor of counterfeit dollars who sells through a darknet market. ‘Benjamin’ (gender unknown) introduces themselves in what becomes a long thread where buyers return to critique their product. Benjamin responds by defending the product, saying that buyers are using it improperly, and eventually agreeing that the counterfeit notes are not what they were. External third-party websites will be presented in a new and separate content window.
Given the rising cybercrime trends, businesses must recognize how cybersecurity risk assessments can help mitigate the dangers posed by dark web scams. The research also revealed that during this time, the number of unique actors selling these fake bills increased by approximately 82%. New research from cybersecurity firm cybersixgill has revealed that 2022 saw an increase of approximately 91% in deep and dark web market listings advertising counterfeit banknotes. In their discussion the buyers mentioned how they slipped the counterfeits into the supply chain. Buying a small value item with $50 or $100 notes and obtaining change would do that. However there was a risk that cashiers would be more likely to scrutinise or refuse large value notes for small value items.
Holding And Placeholder Prices

For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. For example, it maintains your privacy and enables you to access untraceable content and services. Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. It is easily accessible by the general public and requires no special configuration.
History Of Dark Web Marketplaces

The weighted mean is the result of taking the sum of the product of the category price and the number of listings of the same category, divided by the total number of listings. Thus, each mean is weighted by the number of listings available in each product category. Active for a decade since 2014, it is a widely used credit card shop used to source stolen credit card information such as dumps, CVVs, Wholesale Accounts. ALEXANDRIA, Va. – A Utica, New York man pleaded guilty yesterday to charges relating to his sale of over $1.2 million in opioid pills and counterfeit U.S. currency on multiple dark web criminal marketplaces.
Illicit Activities And Virtual Assets
It found that the top three searches were for cloned credit cards of American Express, Mastercard and VISA. A cloned card is a type of credit card theft where a person’s card information is copied into a new card, which allows the scammer to access their financial accounts. While the internet has become a part of daily life for most people, be it at work or at home to relax, it’s become more dangerous with the rise of AI, crypto scams, banking copycat websites, fake dating profiles and investment scams. You never know when one click could lead to your personal information getting hacked, or your hard-earned money slipping away.
Market Infiltration And Undercover Operations
In addition to money laundering, the dark web is also a breeding ground for various financial fraud schemes. One prevalent form of financial fraud on the dark web is identity theft, where criminals steal personal information such as social security numbers, credit card details, and bank account information to commit fraudulent activities. In recent years, the internet has become a breeding ground for illegal activities, and one of the most alarming trends is the sale of counterfeit money online.
To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web. The only difference is that it passes your traffic through random nodes before reaching the destination. This means your activities cannot be traced or your browser history exposed. As listed above in our article, even respected organizations like the BBC and ProPublica have a version of their site on the dark web. Onion links have no regular domain names registered under the domain name registry.
Immediately close your entire Tor Browser window (not just that active tab). Note that engaging with the content in any way is not only distressing but could also put you at legal risk. Your online activity and communications remain private and secret on the dark web. Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons. With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential. It is a good way to prevent third parties from tracking online activities.