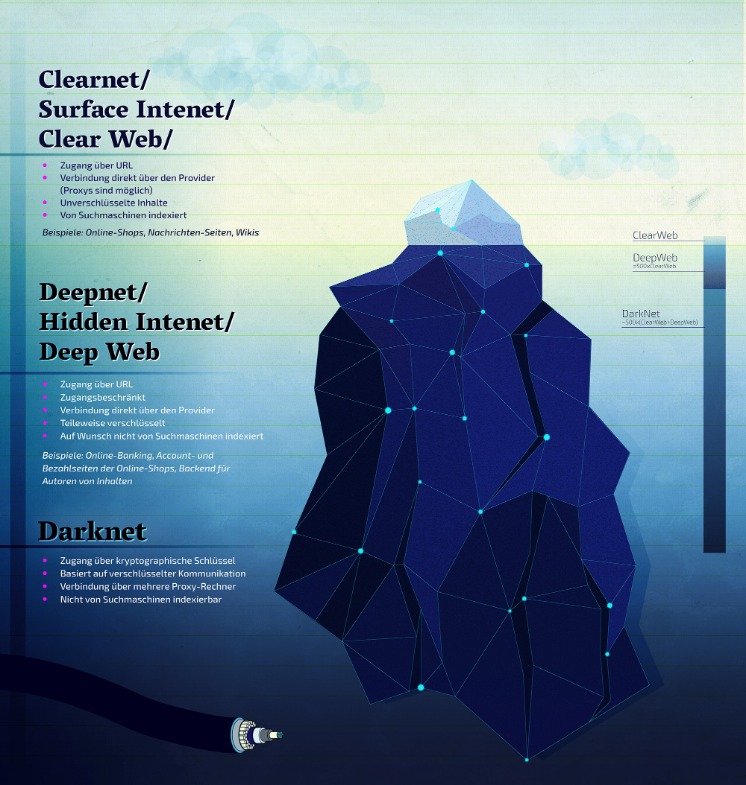
In the summer of 2017, a team of cyber cops from three countries successfully shut down AlphaBay, the dark web’s largest source of contraband, sending shudders throughout the network. The terms “deep web” and “dark web” are sometimes used interchangeably, but they are not the same. Deep web refers to anything on the internet that is not indexed by and, therefore, accessible via a search engine like Google. Deep web content includes anything behind a paywall or requires sign-in credentials.
The CSO Guide To Top Security Conferences
Leveraging these essential tools with caution and awareness will greatly enhance your ability to find dependable .onion links and navigate the dark web safely. Using NordVPN or even ExpressVPN or PIA seems to be beneficial for many users. Such providers offer strong encryption and don’t store logs, ensuring all online footsteps are completely masked. Above all, it’s vital to go on the dark web carefully and sensically. PIA is popular in the USA because it offers servers in all 51 states. People in the United States and abroad can use it to venture into the dark web in privacy.
Dark Web Search Engines
Consequently, previously active .onion addresses abruptly stop working, leaving users searching for new, trustworthy sources. The Tor network understands these addresses by looking up their corresponding public keys and introduction points from a distributed hash table within the network. It can route data to and from onion services, even those hosted behind firewalls or network address translators (NAT), while preserving the anonymity of both parties.
Formerly, Darren served on the Committee of Technology Infrastructure under Mayor Richard Daley. Even completing a transaction is no guarantee that the goods will arrive. Many need to cross international borders, and customs officials are cracking down on suspicious packages. The dark web news site Deep.Dot.Web teems with stories of buyers who have been arrested or jailed for attempted purchases. Many dark websites are set up by scammers, who constantly move around to avoid the wrath of their victims. Even commerce sites that may have existed for a year or more can suddenly disappear if the owners decide to cash in and flee with the escrow money they’re holding on behalf of customers.

What Services And Tools Are Available On The Dark Web?
CiviCRM, an open-source software used by the Tor Project to manage donor data and communications, offers full system control to handle donor data securely with confidence. To turn it on, just go to the “Settings” and then the “Tools” section of the NordVPN app and activate “Dark Web Monitoring.” In the end, it’s all about staying one step ahead. The more proactive you are, the better you can protect yourself against identity theft and other cyber threats. They’re tightening security and carefully screening anyone who wants to join.
The so-called surface web is readily accessible to all of us and thereby, less interesting. Well, relying on Tor to keep you anonymous online is a good recipe for disaster – we’ll see why soon. Tor Browser is a web browser designed to enable anonymous communication and browsing on the internet.
Can I Go On The Dark Web On My IPhone?
That means that even if an ISP is monitoring all of the known Tor relays, they may not be able to block all of the obfuscated bridges. One of the major advantages of using Tor in overly-restrictive countries is that it keeps your online travels private. Unfortunately, some oppressive regimes have figured out a way to block Tor traffic. Using a VPN in conjunction with the Tor Browser is an excellent way to keep your online travels secure and private.
Can You Be Tracked If You Use Tor With A VPN?
- Just bypass your standard web browsers and fire up your tor browser to get on the dark web to access one of the best tor sites.
- Although the social application is known for collecting data on its platform, it does not like sharing the information with others.
- The release of Freenet in 2000 is considered by many as the start or founding of the dark web.
- However, if you’re looking to trade or buy something, the risk of scams increases exponentially.
- Unlike other search engines, it does not collect or share web activities and personal data of users.
- Formerly known as Archive.is, it is one of the best onion sites on the dark web.
Naval Research Laboratory mathematicians and computer scientists in the mid-1990s. The U.S. Army developed “onion routing” to protect intelligence communications online. The dark web is infamous for containing sites such as Silk Road and other marketplaces where users could potentially buy drugs and/or weapons, stolen credit cards, IDs, and much more. The dark web (often referred to as the “dark net”, “black web”, or “black net”) is a small section of the deep web that is hidden and kept inaccessible to regular internet users on purpose. First, let me explain that this article is intended for users who want to use the dark web for legal and needed purposes, such as finding censored news, blocked websites, and other much-needed services. The content of all these pages is stored on Google’s servers, but it’s mostly outdated, old content; smartphone app content; journals; court records; private social media profiles, and much more.
- Such providers offer strong encryption and don’t store logs, ensuring all online footsteps are completely masked.
- While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings.
- It’s also a marketplace for digital mercenaries; you’ll find everything from solo hackers offering their skills to well-organized groups that take on more complex or high-stakes projects.
- The dark web serves as a common platform for cybercriminals to distribute various types of malicious software designed to compromise users’ devices and steal their personal information.
- The dark web isn’t just one sketchy marketplace hiding in a corner of the internet; it’s more like a messy, unregulated community with everything from freedom fighters to full-blown cybercriminals.
- The question of how to look for information in the scary and super dupper dark corner of the Internet.
Criminal Hacking Services
By providing alternative paths to valuable resources, mirror sites help users avoid disruption and maintain secure and consistent access to essential information or services. In contrast, .onion email providers are specifically designed for the Tor network. They provide a layer of encryption and heightened privacy, ensuring that your identity and location remain confidential. These services do not expose your information to the wider internet, which can significantly reduce the risk of surveillance or data breaches. By using .onion email providers, you not only align with the privacy-oriented ethos of Tor but also enhance your overall online security.
More curated and potentially safer directories include Tor Taxi and Dark Fail, which often attempt to vet the links they provide. However, even these resources are not immune to compromise or the inclusion of malicious links, so a degree of skepticism is always warranted. While it’s generally safe to use, dark web activity can be detected at the entry and exit nodes of the Tor network. Darknet or dark web marketplaces are a hidden part of the internet that surface web users can’t access; they can only be accessed with special anonymity software called Tor.
A Dark Web Search Engine

This type of government surveillance applies mostly to countries with environments that are hostile to free speech. Unfortunately, it’s also a place where the bad guys can offer their services – for example, hackers or hitmen. In opennet mode, the network will automatically assign you to other users on Freenet’s network. Supreme Court will allow the FBI to search and seize any computer that’s using the Tor browser or VPN. Rule No.41 allows a federal judge to issue a search and seize warrant for any person who is using anonymity software like Tor. Click on “Safest.” As you’ll see, JavaScript and a few other features will be automatically disabled on all sites.

If someone has the market’s code to the infrastructure, no matter how much effort law enforcement puts in, it will keep coming back on another server or can be built again with the same branding. From there, these products are then passed on to distributors, which are the dark web marketplaces in this context. On these marketplaces, they’re listed, sold, and promoted just like items on any e-commerce site. On the dark web, you don’t need to be a technical expert to design ransomware, and that’s dangerous. Even people with little to no knowledge can buy ready-made ransomware and launch attacks on their victims.



